Incorporating security activities into the natural workflow of productive tasks, makes it easier for people to adopt new technologies and ways of working, but it’s not necessarily enough to guarantee that you’ll be able to solve a particular security-usability issue. The reason for this is that such problems can be categorised as wicked.
Rittel and Webber in ‘Policy Sciences’ define a wicked problem in the context of social policy planning as a challenging – if not impossible – problem to solve because of missing, poorly defined or inconsistent requirements from stakeholders, which may morph over time and which can be demanding to find an optimal solution for.[1]
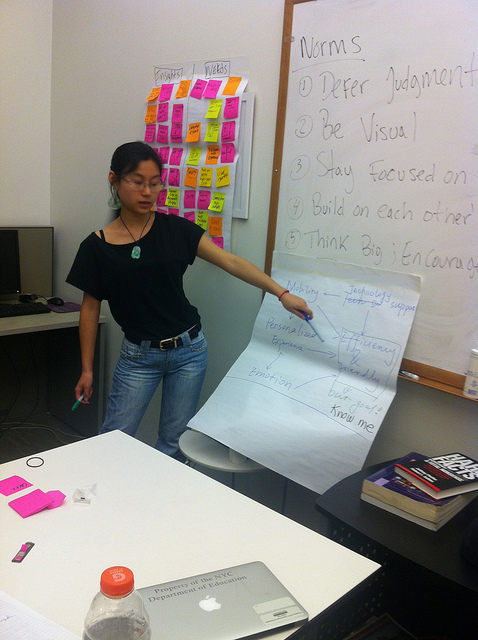
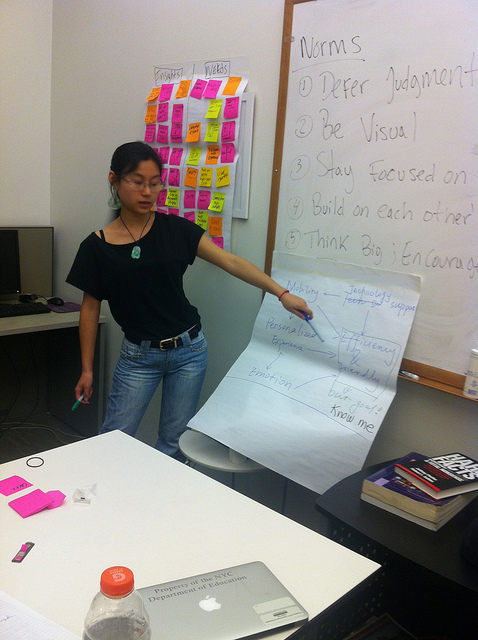
One cannot apply traditional methods to solving a wicked problem; a creative solution must be sought instead. One of these creative solutions could be to apply design thinking techniques.
Methods for design thinking include performing situational analysis, interviewing, creating user profiles, looking at other existing solutions, creating prototypes and mind mapping.
Plattner, Meinel and Leifer in ‘Design Thinking: Understand–Improve–Apply’ assert that there are four rules to design thinking, which can help security professionals better approach wicked problems:[2]
- The human rule: all design activity is ultimately social in nature.
- The ambiguity rule: design thinkers must preserve ambiguity.
- The redesign rule: all design is redesign
- The tangibility rule: making ideas tangible always facilitates communication.
Security professionals should adopt these rules in order to develop secure and usable controls, by engaging people, utilising existing solutions and creating prototypes that can help by allowing the collection of feedback.
Although this enables the design of better security controls, the design thinking rules rarely provide an insight into why the existing mechanism is failing.
When a problem occurs, we naturally tend to focus on the symptoms instead of identifying the root cause. In ‘Toyota Production System: Beyond Large-Scale Production’, Taiichi Ohno developed the Five Whys technique, which was used in the Toyota production system as a systematic problem-solving tool to get to the heart of the problem.
In one of his books, Ohno provides the following example of applying this technique when a machine stopped functioning:[3]
- Why did the machine stop? There was an overload and the fuse blew.
- Why was there an overload? The bearing was not sufficiently lubricated.
- Why was it not lubricated sufficiently? The lubrication pump was not pumping sufficiently.
- Why was it not pumping sufficiently? The shaft of the pump was worn and rattling.
- Why was the shaft worn out? There was no strainer attached and metal scrap got in.
Instead of focusing on resolving the first reason for the malfunction – i.e. replacing the fuse or the pump shaft – repeating ‘why’ five times can help to uncover the underlying issue and prevent the problem from resurfacing again in the near future.
Eric Reis, who adapted this technique to starting up a business in his book The Lean Startup,[4] points out that at “the root of every seemingly technical problem is actually a human problem.”
As in Ohno’s example, the root cause turned out to be human error (an employee forgetting to attach a strainer), rather than a technical fault (a blown fuse), as was initially suspected. This is typical of most problems that security professionals face, no matter which industry they are in.
These techniques can help to address the core of the issue and build systems that are both usable and secure. This is not easy to achieve due to the nature of the problem. But, once implemented, such mechanisms can significantly improve the security culture in organisations.
References:
[1] Horst W. J. Rittel and Melvin M. Webber, “Dilemmas in a General Theory of Planning”, Policy Sciences, 4, 1973, 155–169.
[2] Hasso Plattner, Christoph Meinel and Larry J. Leifer, eds., Design Thinking: Understand–Improve–Apply, Springer Science & Business Media, 2010.
[3] Taiichi Ohno, Toyota Production System: Beyond Large-Scale Production, Productivity Press, 1988.
[4] Eric Reis, The Lean Startup, Crown Business, 2011.
Image by Paloma Baytelman https://www.flickr.com/photos/palomabaytelman/10299945186/in/photostream/
To find out more about the psychology behind information security, read Leron’s book, The Psychology of Information Security. Twitter: @le_rond