In order to ensure the security of a system sometimes it is not enough to follow the general advice outlined in the Overview of Protection Strategies and one may chose to perform a penetration test.
Security assessments of this highly sensitive environment should be conducted with extreme care. It requires not only basic network security skills but also knowledge of the equipment, SCADA-specific protocols and vulnerabilities.

On the photo you can see different types of PLC and RTU devices, discussed in the Overview of Industrial Control Systems:
- Modicon Momentum PLC
- Rockwell Automation MicroLogix 1100 PLC
- Siemens S7 1200 PLC
- Small embedded RTU device
The original SCADA protocols (vendor-specific protocols include ModbusRTU, DF1, Conitel, and Profibus) were serial-based, meaning that the master station initiated the communication with the controllers. Nowadays, almost all SCADA protocols are encapsulated in TCP/IP and can be operated over Ethernet.
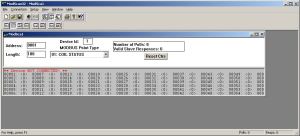
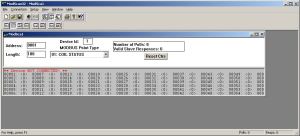
To get a better understanding, one can use Modscan32 to connect to the PLC and view register data by entering the IP address and TCP port number in the tool.
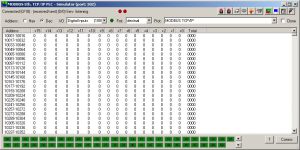
If there is no live PLC available to work with, one can always use the ModbusTCP simulator to practice capturing traffic with Wireshark, configuring the OPC server and building human-machine interfaces.