ArchiMate modelling language is one of the The Open Group enterprise architecture standards. It is aligned with TOGAF and aims to help architects (and other interested parties) understand the impact of design choices and changes.
I provide a high-level overview of this standard and the free open-source modelling tool used to describe, analyse and visualise architecture in my previous blog.
Here I would like to build on the foundation we’ve laid while discussing SABSA architecture and design case study and share and example of using the Archi tool to model security architecture using the SABSA framework.
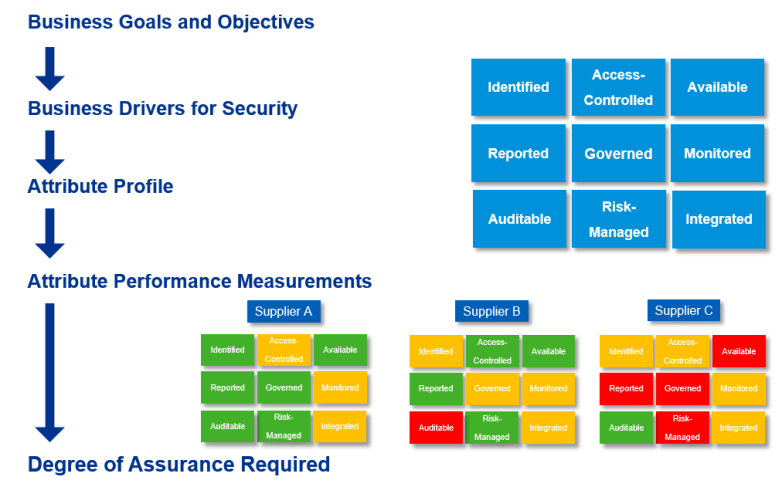
Let’s say ACME Corp asked us to help them with their security architecture. Where do we start?
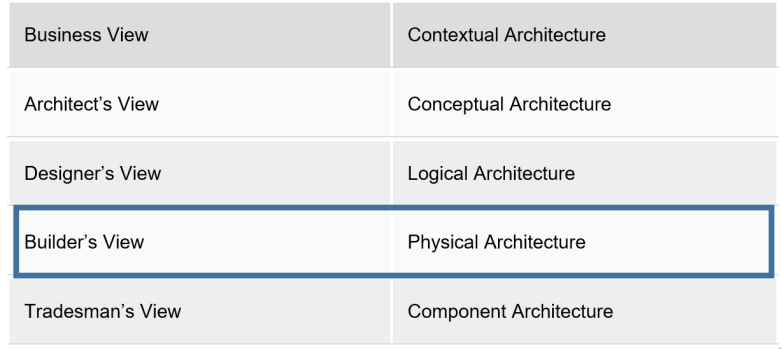
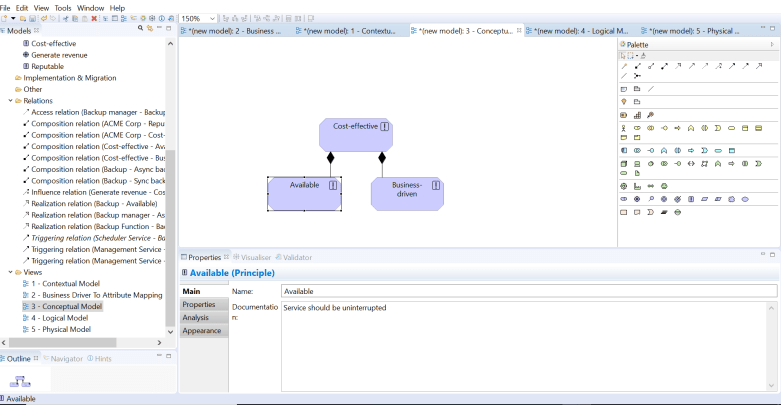
As described in my previous blog, let’s establish Contextual Architecture.
Using Archi, I select Principles (can be found in Motivation section) for attributes and define composition relationship between elements (e.g. ACME Corp is composed of Cost-effective, Reputable and many other attributes that hopefully define the business).
Here and below I’ll be using a simplified example just to illustrate a point – you will have many more attributes in practice.
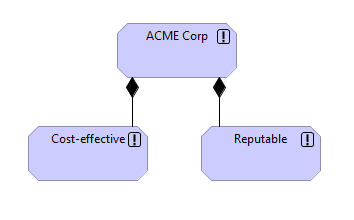
From reading company annual reports and talking to business stakeholders we can start identifying business drivers of ACME Corp. We can them map these business drivers to attributes. Below is an illustration of mapping a business driver Generate revenue (Driver element) to the attribute Cost-effective using Influence relation, as business drivers influence attributes.
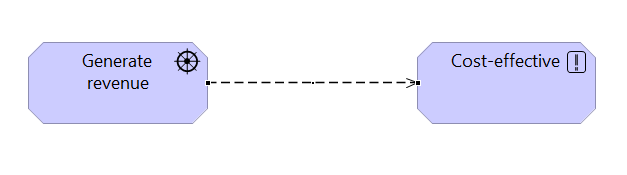
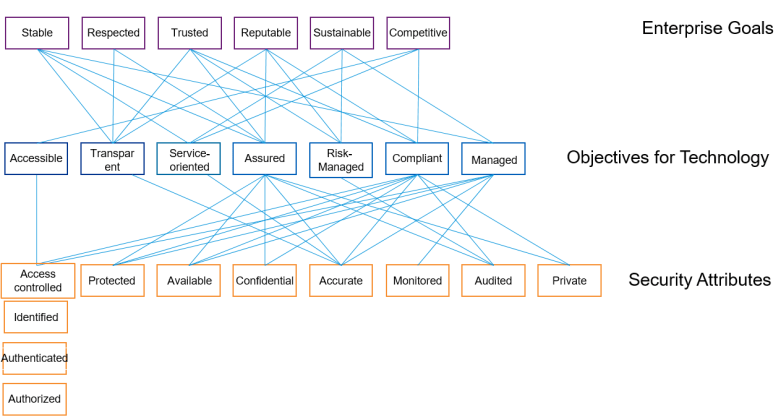
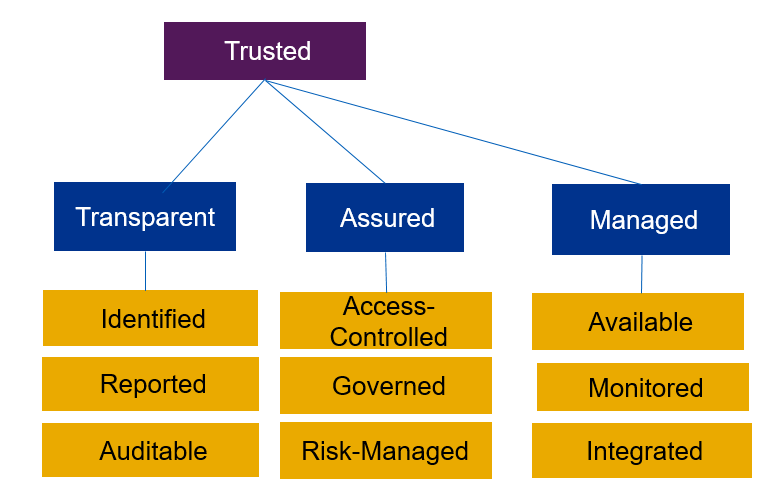
On the Conceptual architecture level we need to start defining lower level attributes. For example, Cost-effective is composed (Composition relation) of Available and Business-driven
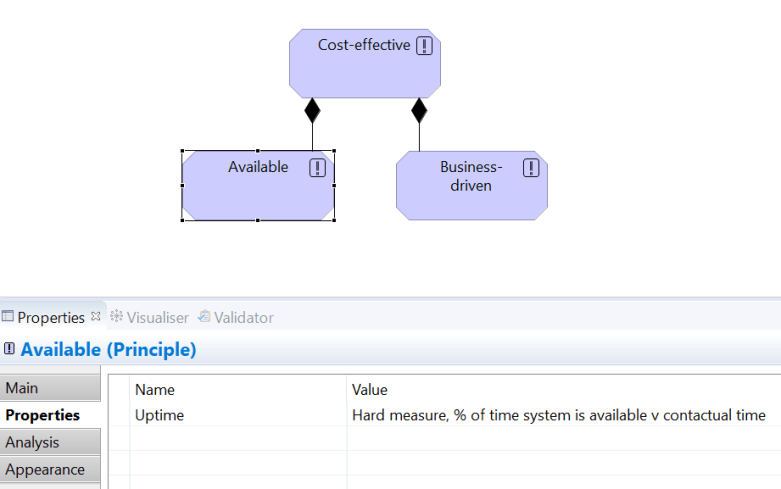
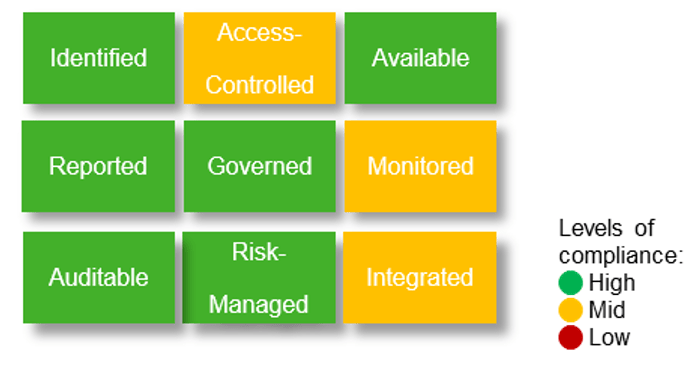
Remember that you can provide definitions of your attributes in the element’s properties (Main section). In this example I’m defining Available as Service should be uninterrupted. You are also encouraged to establish a measurement approach for each attribute. You can see above that Uptime is the main KPI for availability. It’s a hard measure where we monitor the percentage of time system is available compared to what is specified in the SLA.
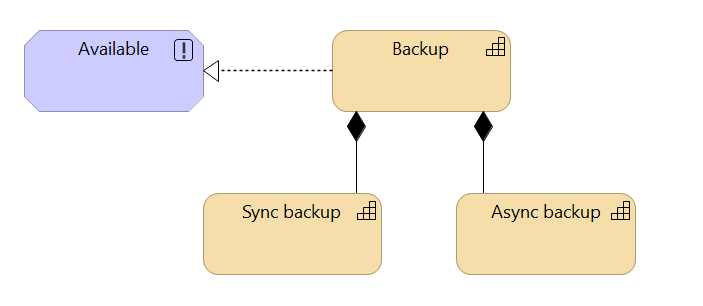
Logical level provides an insight into what capabilities enable the attributes. In the example below, Available is realised (Realisation relation) by Backup capability which in turn is comprised of Synchronous and Asynchronous backup capabilities (Composition relation).
Archi tool allows us to model SABSA Physical Architecture view by describing services, events, processes, interfaces, functions and other elements of the TOGAF Technology layer.
Below is a simplified example of describing the Asynchronous backup capability.
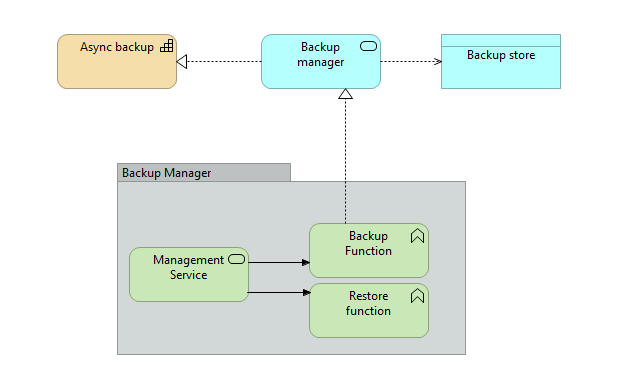
Asynchronous backup is being realised by Backup manager application service (realisation relation). Backup store is a data object that is being accessed by the Backup manager (access relation).
You can be quite detailed here and that’s where Archi tool can add a lot of value. But to keep things simple, I’m going to leave it at that. You can decompose elements into services and function, group them together and even go lower describing actual technology solutions on SABSA Component architecture level.
The real question is: what do you do with all of this?
My answer is simple: visualise.
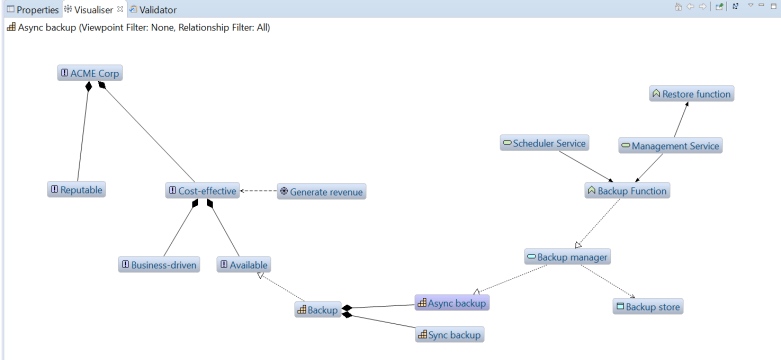
Archi lets you switch into the Visualiser mode and create graphs bringing all your hard work together. Playing with depth (6 in the example above) you can analyse the architecture and ensure traceability: you can see and, more importantly, demonstrate to your business stakeholders how a particular technology solution contributes to the overall business objective.
In addition, the Validator allows you to see the elements that are orphaned, i.e. not related to any other element. You then have the ability to rectify this and introduce a relationship or discontinue the capability (otherwise, why are you paying for something that is not in use?).
If you followed the steps above, the tool, despite being free, actually does a lot of the heavy lifting for you and automatically adjusts the models and graphs if changes to the architecture are introduced.
Now it’s your turn to try out Archi for SABSA architecture. Good luck!
I would like to thank Chul Choi for outlining the above technique.