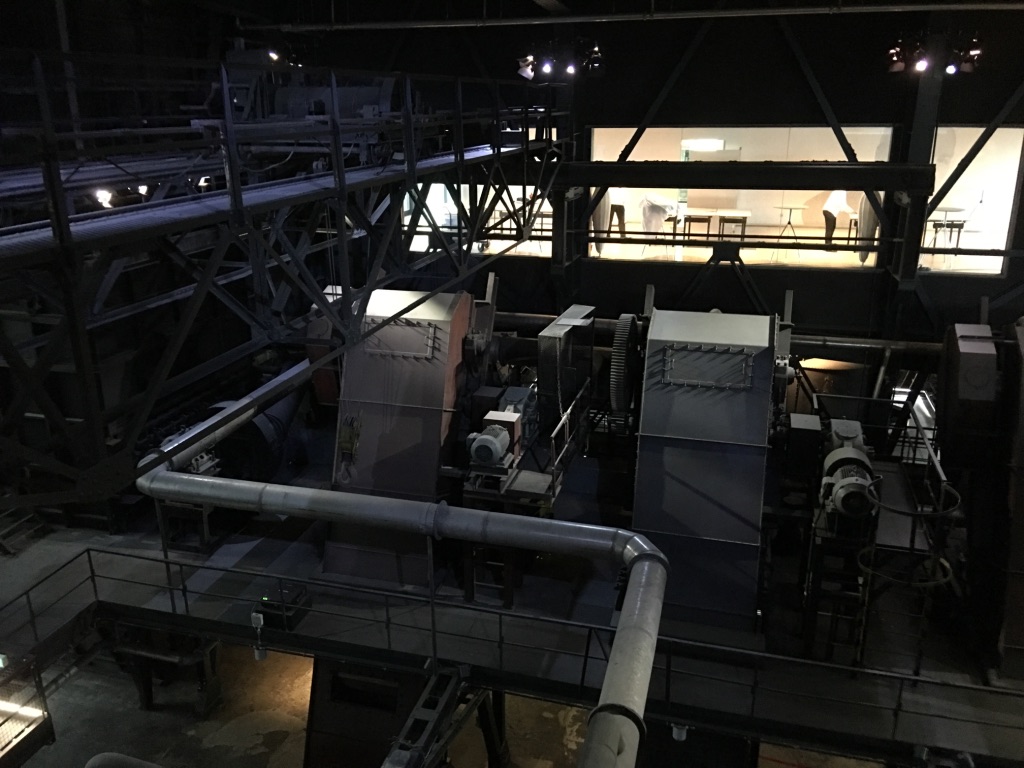
Today’s major industries rely on finely automated industrial control sectors and are operated by critical infrastructures of highly interconnected and mutually dependent systems known as industrial control systems (ICS). These are predominantly found in industries such as transportation, electric, oil and natural gas, utility power, pulp and paper, mining, discrete manufacturing (i.e. durable goods, automotive, aerospace, etc.), chemical, metals, food and beverage, water and wastewater, and pharmaceutical.
The term ICS comprises three main types of systems which include distributed control systems (DCS), supervisory control and data acquisition (SCADA) systems, along with the incorporation of smaller controller hardware components such as the skid-mounted Programmable Logic Controllers (PLC).
DCS are usually found within a localized area, such as an industrial process plant or a factory, as a specific functional distributed control system design that relies on supervisory and regulatory control. DCS emerged as a tool for controlling the systems involved beyond a small cell area, while collecting data in real time on high-bandwidth/low-latency data networks. Because everything operates in real time, loop control will commonly extend up to the DCS top level controllers. Such systems can be found in refineries and chemical plants, among others.
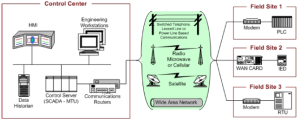
SCADA systems were designed to cater to distribution applications where remote data must be gathered through more unreliable data networks, such as those with low-bandwidth/high-latency links. These systems are implemented in widely separated geographical sites (often scattered over thousands of square kilometers) using an open-loop control, through centralized data acquisition and supervisory control. Supervisory data is typically sent back to a control center through remote terminal units (RTUs), which tend to be restricted to a limited capacity for handling local controls whenever the master station is not available. With technological advances, however, the capability of these RTU systems continues to grow, allowing for better performance. SCADA systems are normally used in water pipelines and natural gas industries, to name a few.
PLCs are computer-based devices and are the result of the technological replacement of relay racks in ladder form. They are the primary components in small control system configuration and are used in almost all discrete industrial processes. PLCs are commonly integrated into DCS architectures as key components that provide feedback or feed forward control loops which automatically maintain the desired conditions of a process around a specific set point. Here, the PLC settings are specified to determine the desired tolerance and provide the rate of self- regulation and self-correction whenever there is a system upset.
Today, the boundaries are blurring between these three system definitions as current ICS architectures are evolving into hybrids that integrate features of both SCADA systems and DCS.
The key components for the operation of an ICS include: a control loop, Human-Machine Interface (HMI) and Remote Diagnostics and Maintenance Utilities (see glossary).
The main control components of an ICS encompass: a control server, a SCADA Server or Master Terminal Unit (MTU), Remote Terminal Units (RTUs), Programmable Logic Controllers (PLCs), Intelligent Electronic Devices (IEDs), a Human-Machine Interface (HMI), a Data Historian and an Input/Output (IO) Server (see glossary).
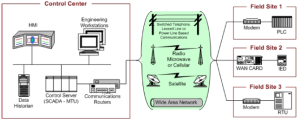
SCADA system general layout (NIST 800-82)
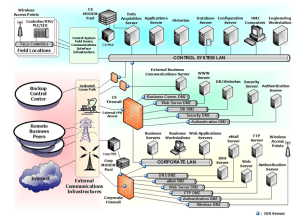
Control networks have merged with corporate networks in order to facilitate monitoring and controlling systems from the outside, which allows decision-makers at an enterprise level have access to process data. Network topologies can vary greatly from ICS to another, with different characteristics for each layer within a control system hierarchy, but the most important components they must include are: a fieldbus network, a control network, communications routers, a firewall, modems, and remote access points.
Originally, ICS used specialized hardware and software to run proprietary control protocols, making them completely isolated systems with little resemblance to traditional information technology (IT) systems. However, in order to facilitate remote access capabilities and corporate connectivity, IT solutions are being designed and implemented into ICS. The use of standard computers, operating systems (OS) and network protocols, along with low-cost Internet Protocol (IP) devices to replace proprietary solutions, provides new IT capabilities, but reduces the ICS isolation from the outside world, thus increasing the possibility of cyber security vulnerabilities and incidents. Despite the availability of solutions to deal with these security issues in typical IT systems, special considerations and precautions must be tailored to secure the ICS. Additionally, efficiency and safety goals can sometimes conflict with security in the design and operation of control systems. Because each one of these ICS is unique in its performance and reliability, each one requires its own unique, and sometimes unconventional, operating system and applications which might be regarded as odd or challenging by typical IT personnel.
The implementation of an ICS always involves some form of impact, which is complex and can go far beyond the immediate processes at hand. Some of the ICS characteristics differ from traditional information processing systems because they affect the physical world directly. These might risk human and environmental health and safety, as well as detonate financial issues related to production losses which can compromise proprietary information and even have a negative impact on a country’s economy.
Glossary
Control loop – contains measurement sensors, controller hardware (such as a PLC), and actuators (such as motors, switches, control valves and breakers), all interconnected, which share the communication of variables. The sensors transmit controlled variables to the controller which then interprets the signals it receives and, based on the set points, manipulates this information to generate new variables. It sends this new information to the actuators which perform accordingly to adjust the system involved into a stated within the set points. Whenever the system or the process is disturbed, the sensors will send new signals to the controller, in order for there to be a readjustment.
Control network – an interconnection between the lower-level control modules and the supervisory control level.
Control server – a host to the supervisory control software of a PLC or DCS that communicates with lower-level control devices. It has access to subordinate control modules within an ICS network.
Data Historian – a centralized database for storing all the ICS process information. This information can be accessed to support statistical process control.
Fieldbus network – a network that connects sensors and other components to a PLC or other controller. Using fieldbus technology eliminates the need for point-to-point wiring between the controller and each device. Communication between the fieldbus controller and the devices is through a variety of protocols. The messages sent between the controller and the sensors identifies each of the sensors uniquely.
Human-Machine Interface (HMI) – these are used by engineers and operators to monitor and configure set points, control algorithms, and establish and regulate parameters in the controller. This interface also displays information on the status of the process, reports, historical information, and other information to administrators, business partners, operators and other authorized users. The platform, interface and location may vary greatly.
Intelligent Electronic Devices (IED) – “smart” devices that combine both sensor/actuator attributes which, when used in SCADA and DCS systems, allow for automatic control at a localized level. They can gather data, communicate with other devices, and perform local processing and control.
Input/Output (IO) Server – a control component that collects, buffers and provides access to process information from control sub-components such as RTUs, IEDs and PLCs. It can be found on the control server or on an independent computer platform. These servers can also be used for interfacing third-party control components such as a control server and an HMI.
Modem – a device that enables communication between components by converting between serial digital data and a signal suitable for transmission over a telephone line. Modems are used in SCADA systems to allow long-distance serial communication between remote field devices and MTUs. They are also used for gaining remote access to operational and maintenance functions in DCS and SCADA systems.
Remote Diagnostics and Maintenance Utilities – are used to identify, prevent and recover from abnormal operation, disruptions or failure.
Remote Terminal Unit (RTU) – (also known as remote telemetry unit) is a control unit for special purpose data acquisition in SCADA remote stations. These field devices support traffic to and from remote sites were wire-based communications are unavailable since they are equipped with wireless radio interfaces.
SCADA Server or Master Terminal Unit (MTU) – this device performs as the master in a SCADA system, in which PLCs and remote terminal units which are located in remote sites act as slaves.
Resources:
Guide to Industrial Control Systems (ICS) Security by NIST
Image courtesy of hin255 / FreeDigitalPhotos.net