Let’s talk about applying the SABSA framework to design an architecture that would solve a specific business problem. In this blog post I’ll be using a fictitious example of a public sector entity aiming to roll-out an accommodation booking service for tourists visiting the country.
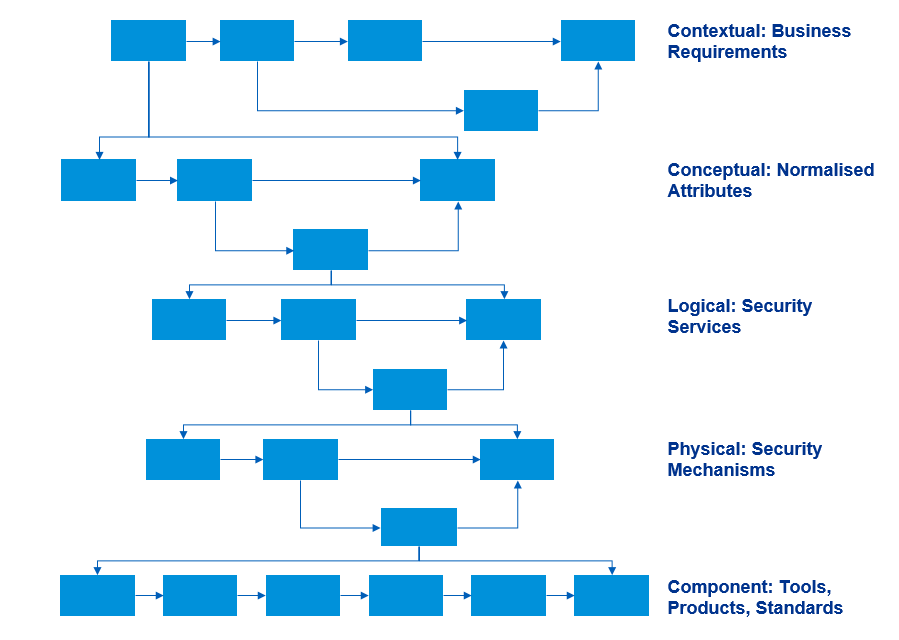
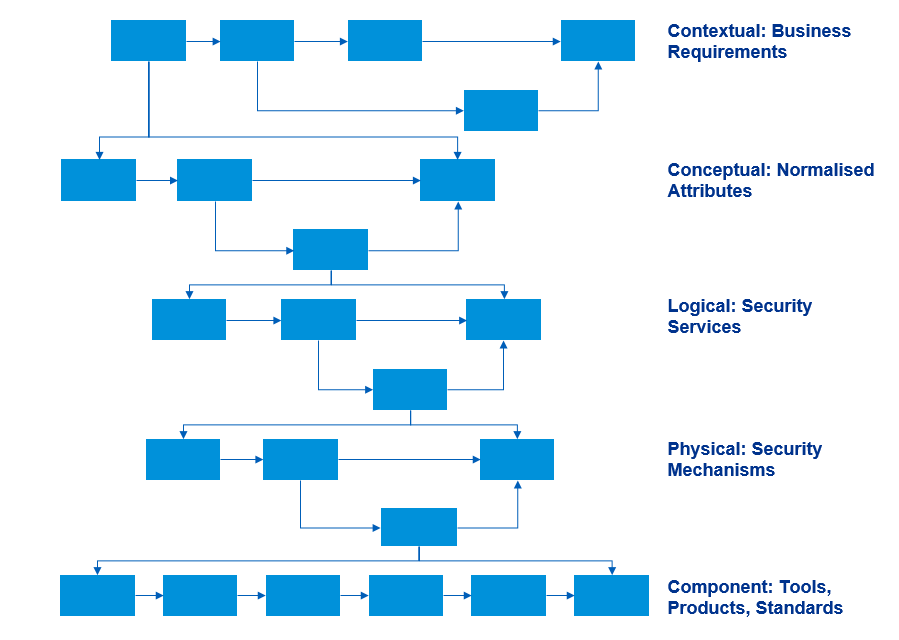
To ensure that security meets the needs of the business we’re going to go through the layers of the SABSA architecture from top to bottom.
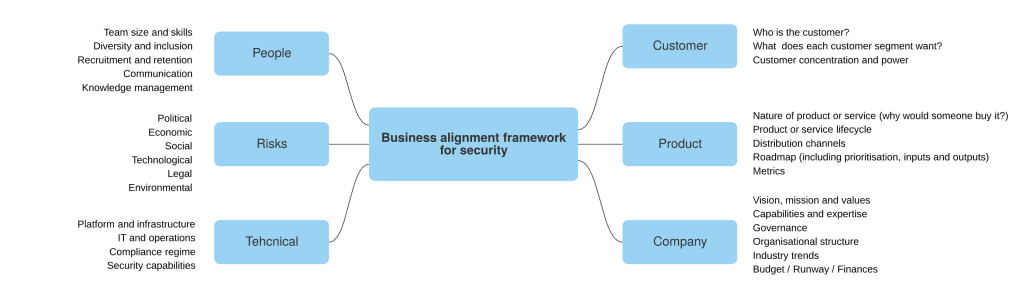
Start by reading your company’s business strategy, goals and values, have a look at the annual report. Getting the business level attributes from these documents should be straightforward. There’s no need to invent anything new – business stakeholders have already defined what’s important to them.
Contextual architecture
Every single word in these documents has been reviewed and changed potentially hundreds of times. Therefore, there’s usually a good level of buy-in on the vision. Simply use the same language for your business level attributes.
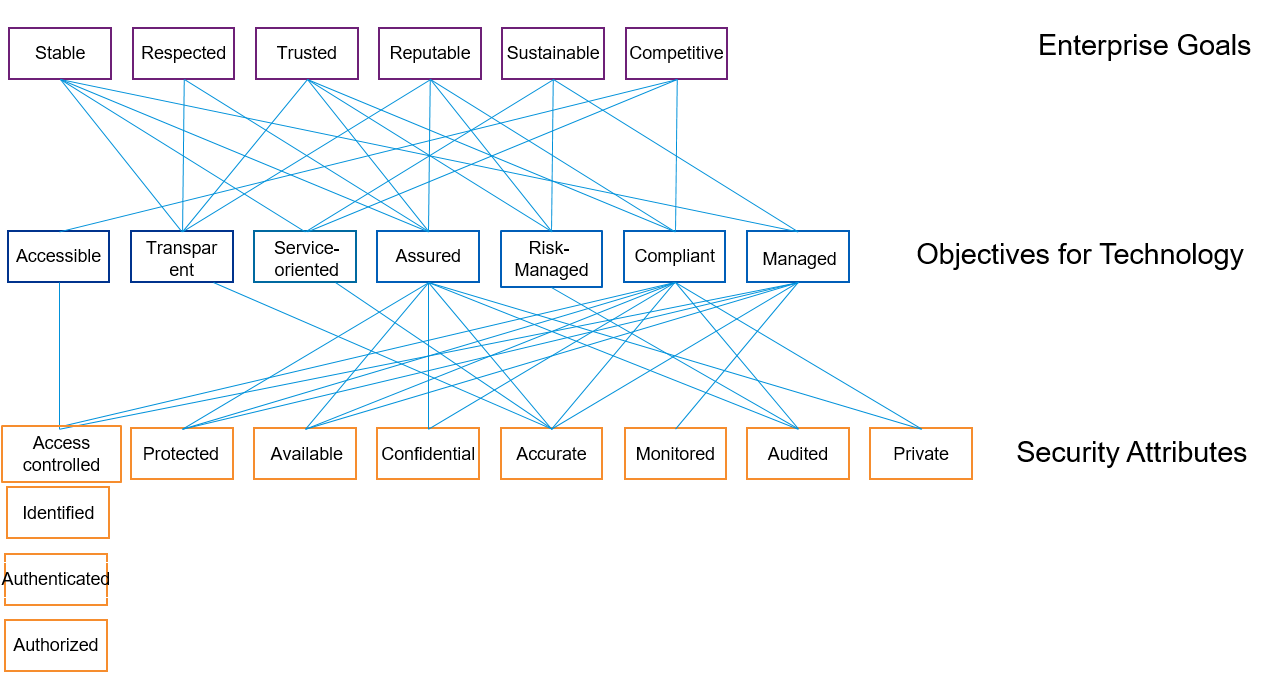
After analysing the strategy of my fictitious public sector client I’m going to settle for the following attributes: Stable, Respected, Trusted, Reputable, Sustainable, Competitive. Detailed definitions for these attributes are agreed with the business stakeholders.
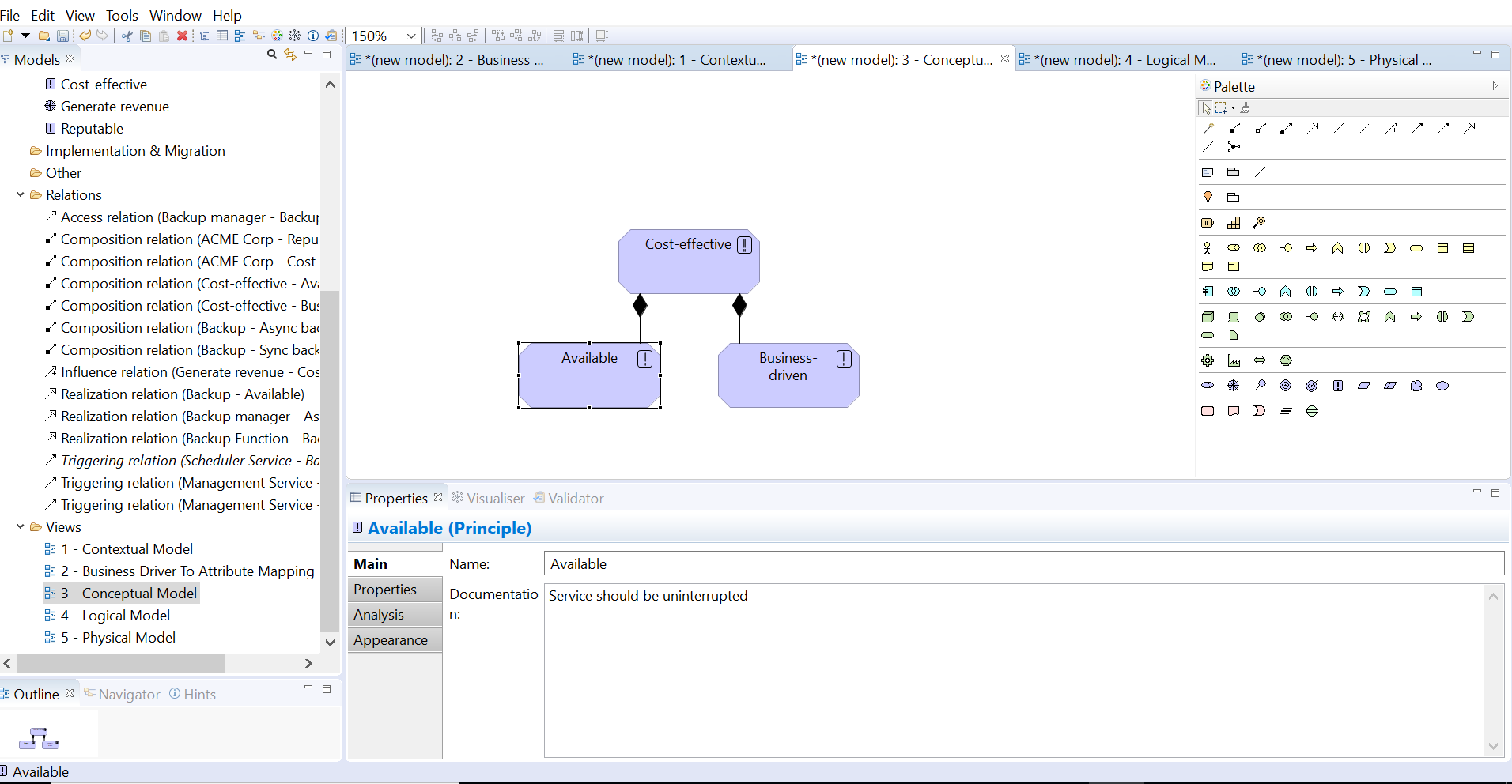
Conceptual architecture
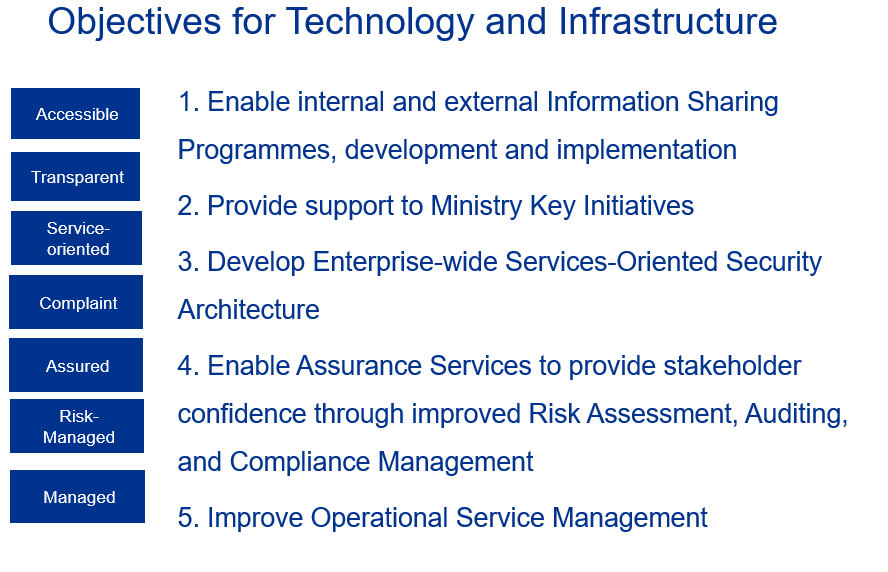
Next step is to link these to the broader objectives for technology. Your CIO or CTO might be able to assist with these. In my example, the Technology department has already done the hard job of translating high-level business requirements into a set of IT objectives. Your task is just distill these into attributes:
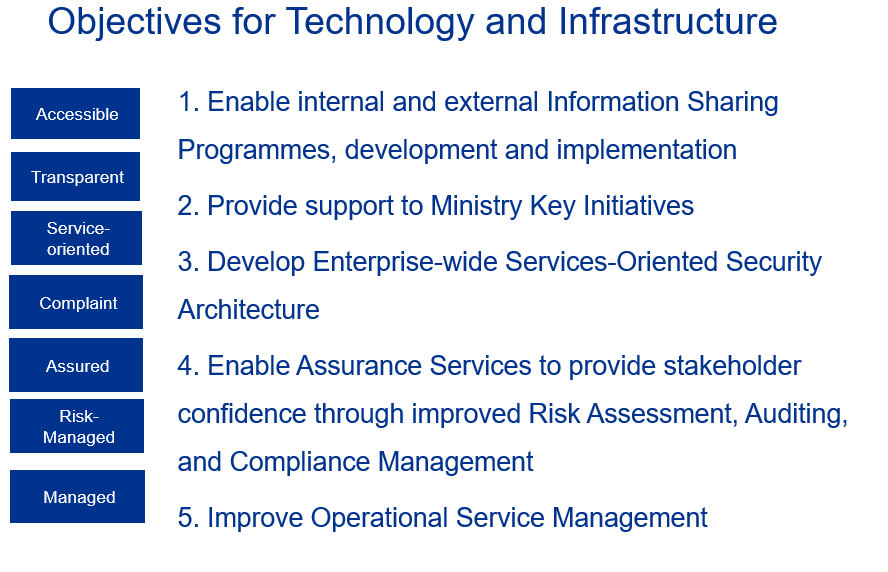
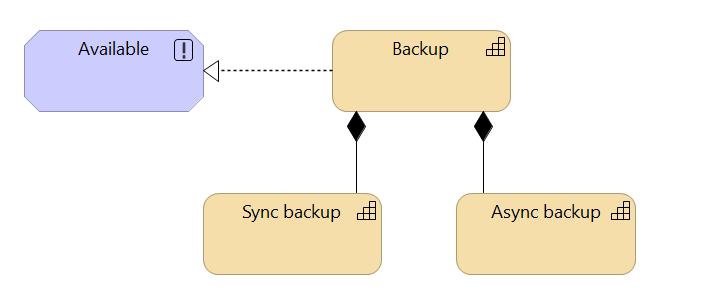
Now it’s up to you to define security attributes based on the Technology and Infrastructure attributes above. The examples might be attributes like Available, Confidential, Access-Controlled and so on.
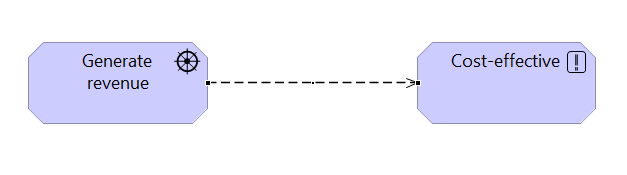
Requirements traceability
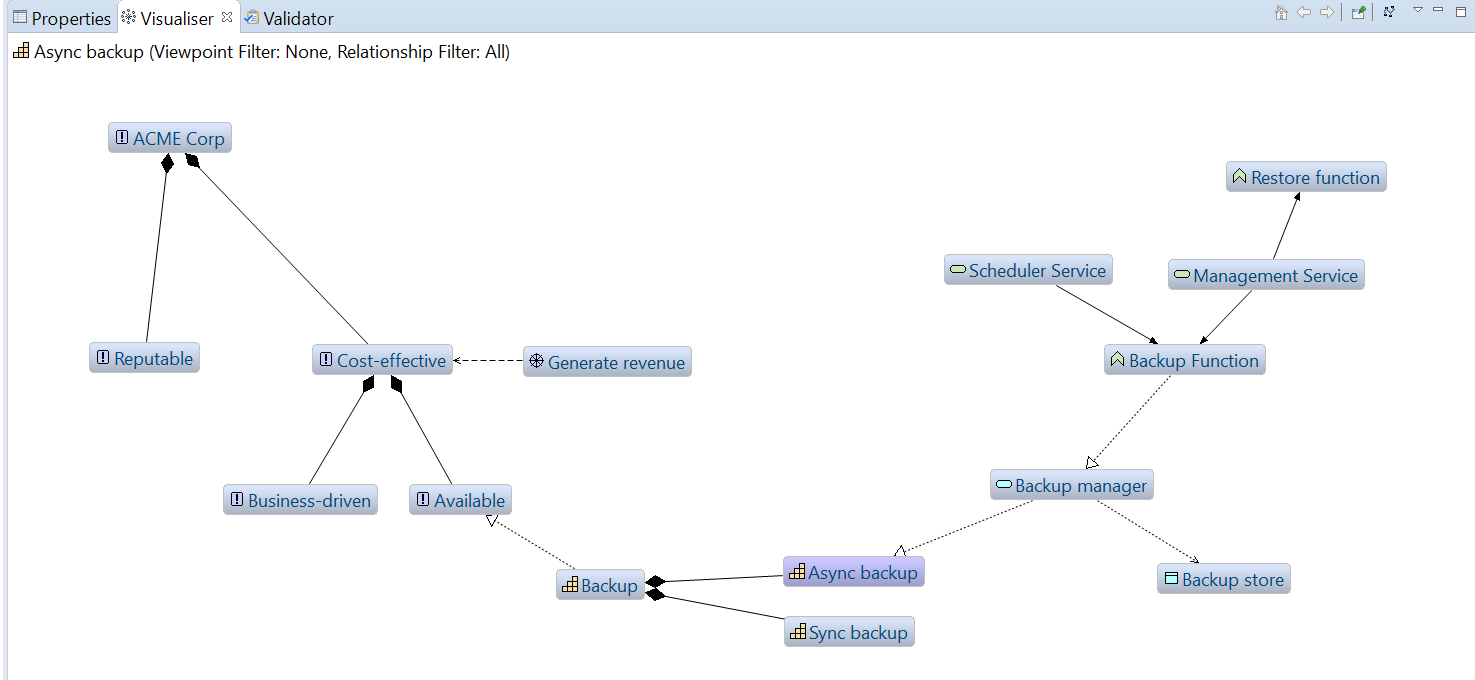
The next step would be to highlight or define relationships between attributes on each level:
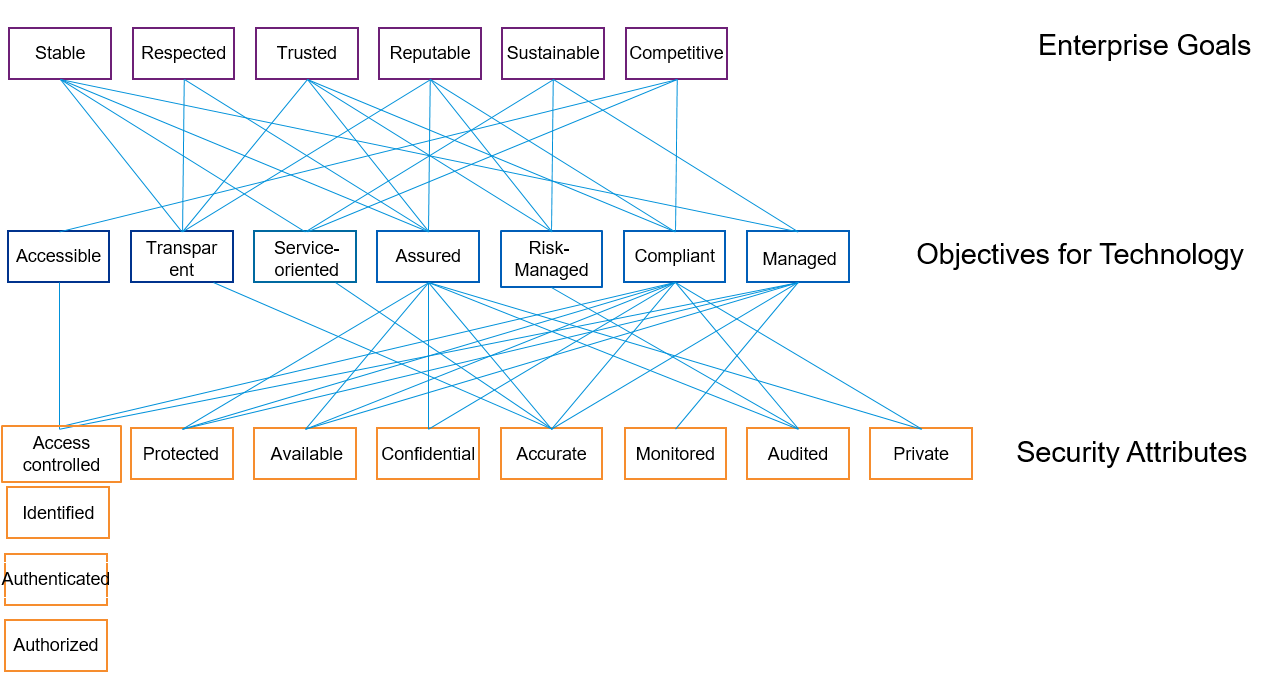
These attributes show how security supports the business and allows for two-way traceability of requirements. It can be used for risk management, assurance and architecture projects.
Back to our case study. Let’s consider a specific example of developing a hotel booking application for a public sector client we’ve started out with. To simplify the scenario, we will limit the application functionality requirements to the following list:
| ID |
Name |
Purpose |
| P001 |
Register Accommodation |
Enable the registration of temporary accommodations available |
| P002 |
Update Availability |
Enable accommodation managers to update availability status |
| P003 |
Search Availability |
Allow international travellers to search and identify available accommodation |
| P004 |
Book Accommodation |
Allow international travellers to book accommodation |
| P005 |
Link to other departments |
Allow international travellers to link to other departments and agencies such as the immigration or security services (re-direct) |
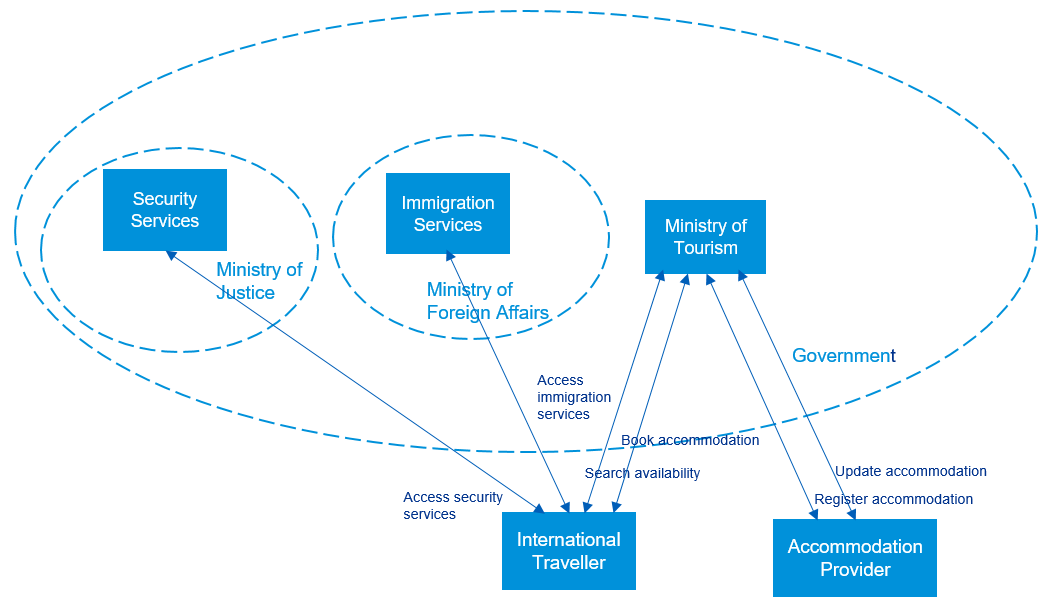
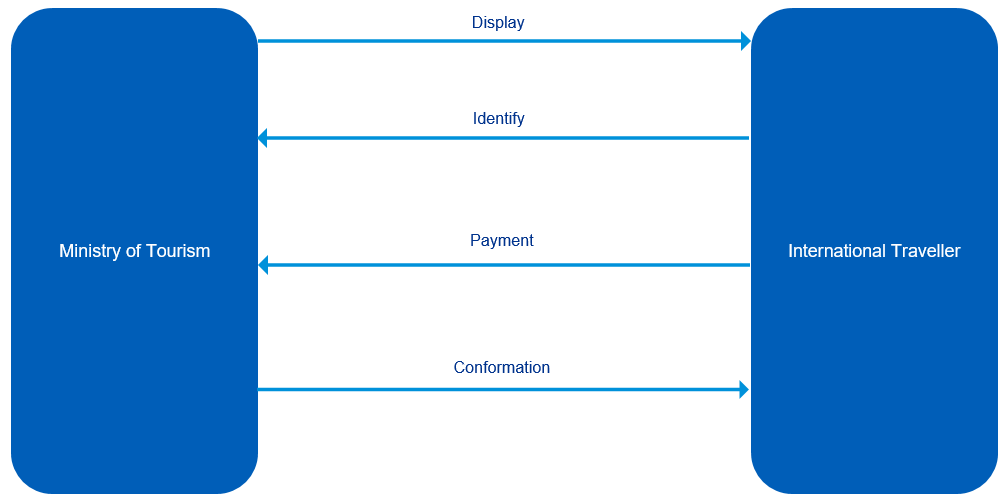
And here is how the process map would look like:
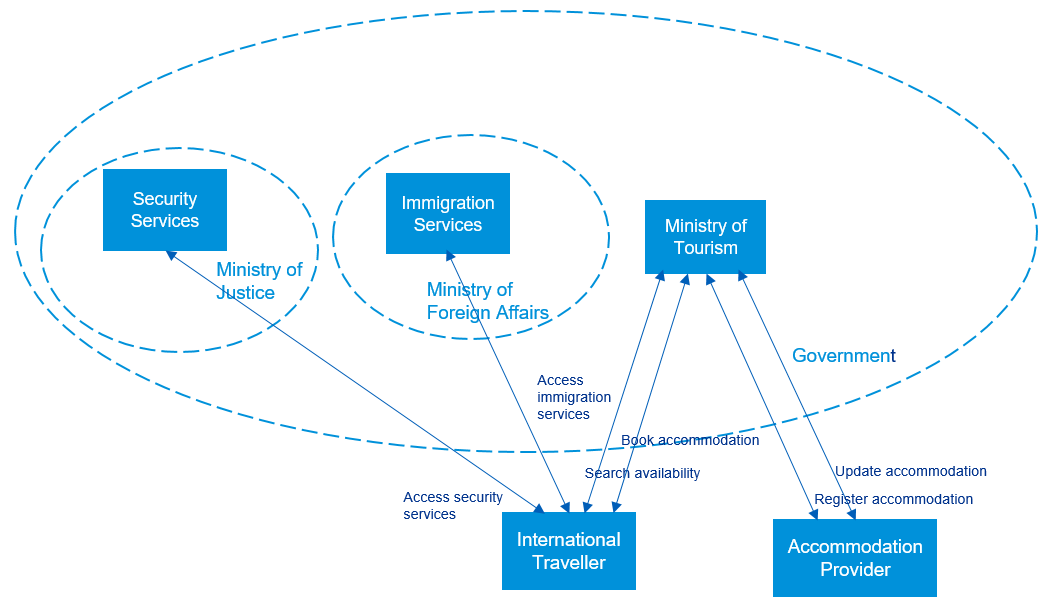
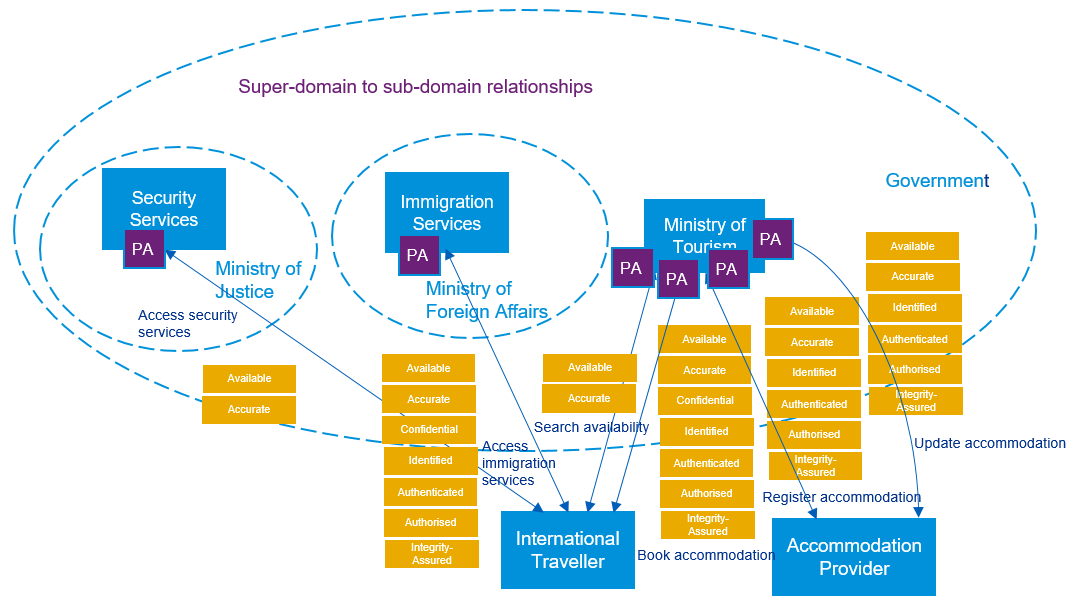
There are a number of stakeholders involved within the government serving international travellers’ requests. Tourists can access Immigration Services to get information on visa requirements and Security Services for safety advice. The application itself is owned by the Ministry of Tourism which acts as the “face” of this interaction and provides access to Tourist Board approved options. External accommodation (e.g. hotel chains) register and update their offers on the government’s website.
The infrastructure is outsourced to an external cloud service provider and there are mobile applications available, but these details are irrelevant for the current abstraction level.
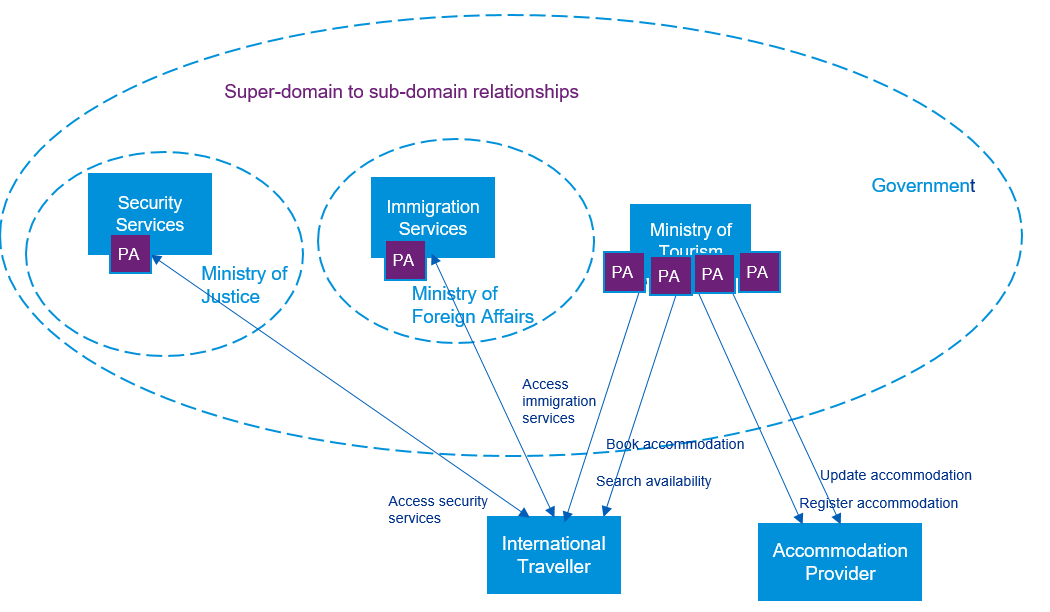
Trust modelling
From the Trust Modelling perspective, the relationship will look like this:
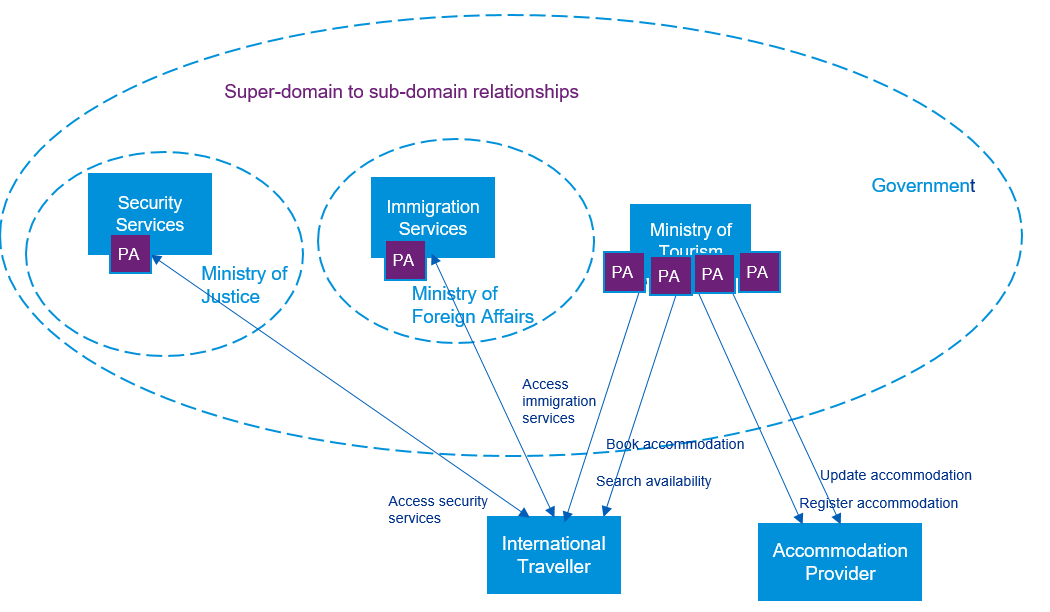
Subdomain policy is derived from, and compliant with, super domain but has specialised local interpretation authorised by super domain authority. The government bodies act as Policy Authorities (PA) owning the overall risk of the interaction.
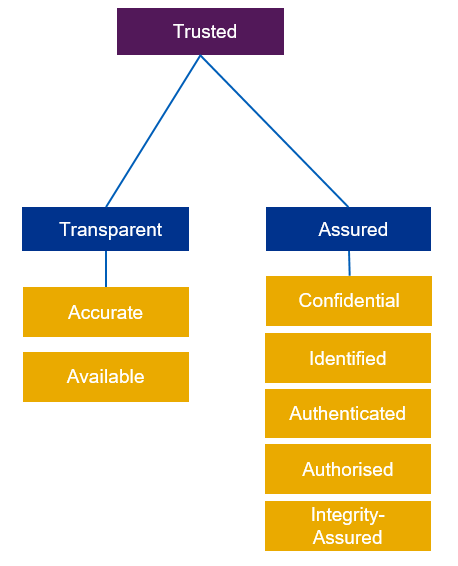
At this stage we might want to re-visit some of the attributes we defined previously to potentially narrow them down to only the ones applicable to the process flows in scope. We will focus on making sure the transactions are trusted:
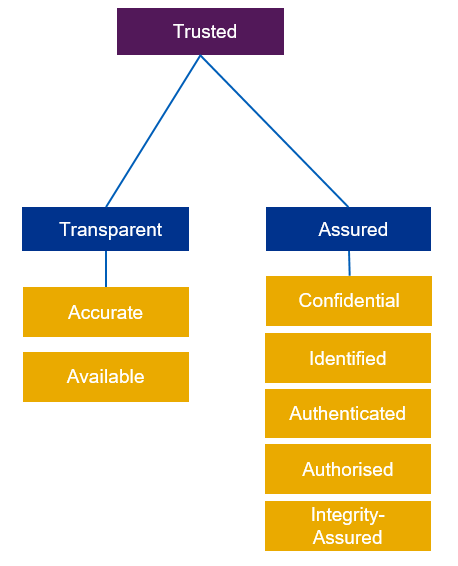
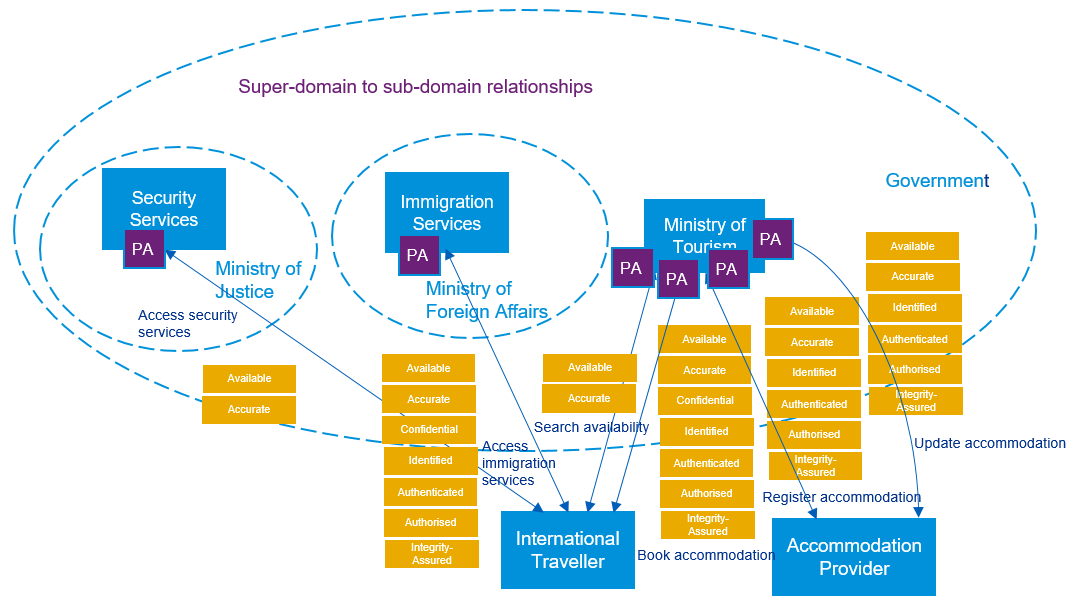
Let’s overlay applicable attributes over process flows to understand requirements for security:
Logical Architecture
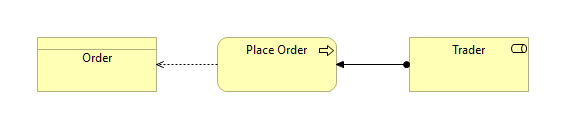
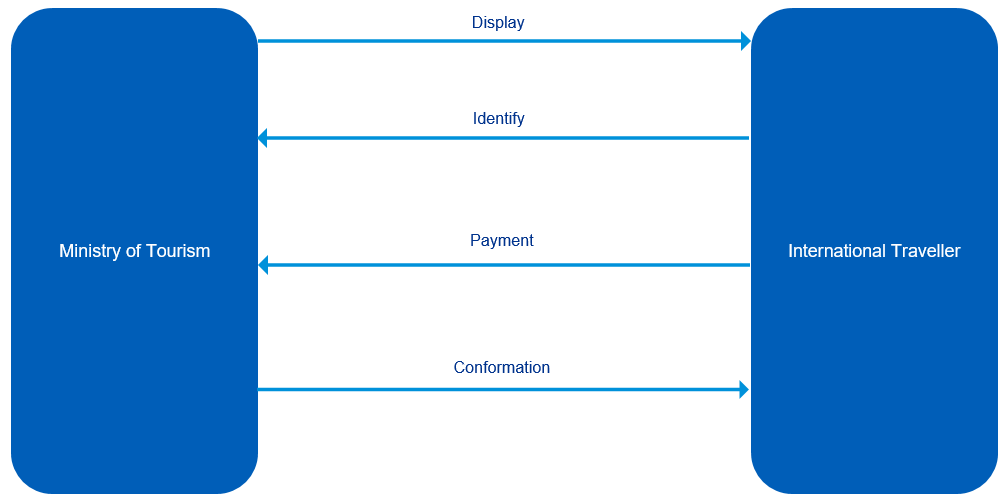
Now it’s time to go down a level and step into more detailed Designer’s View. Remember requirement “P004 – Book Accommodation” I’ve mentioned above? Below is the information flow for this transaction. In most cases, someone else would’ve drawn these for you.
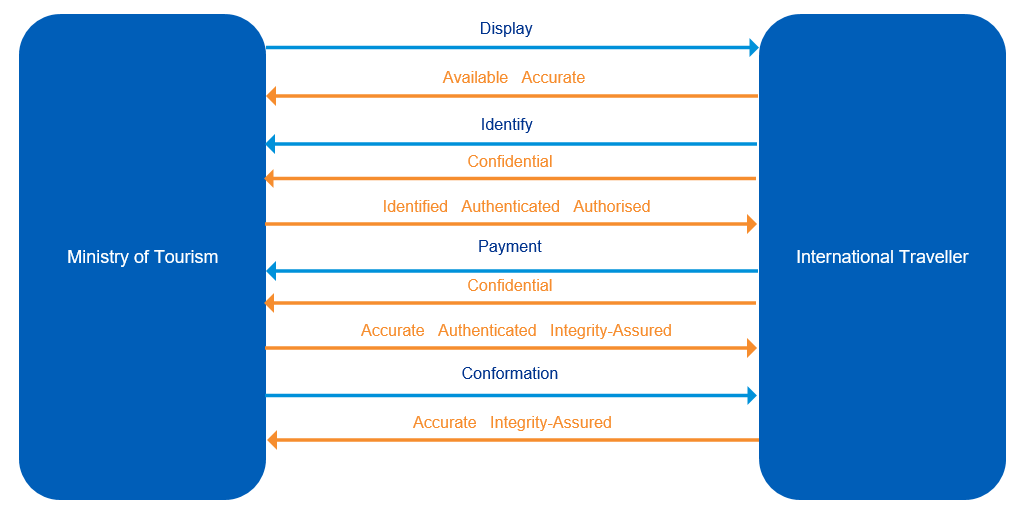
With security attributes applied (the direction of orange arrows define the expectation of a particular attribute being met):
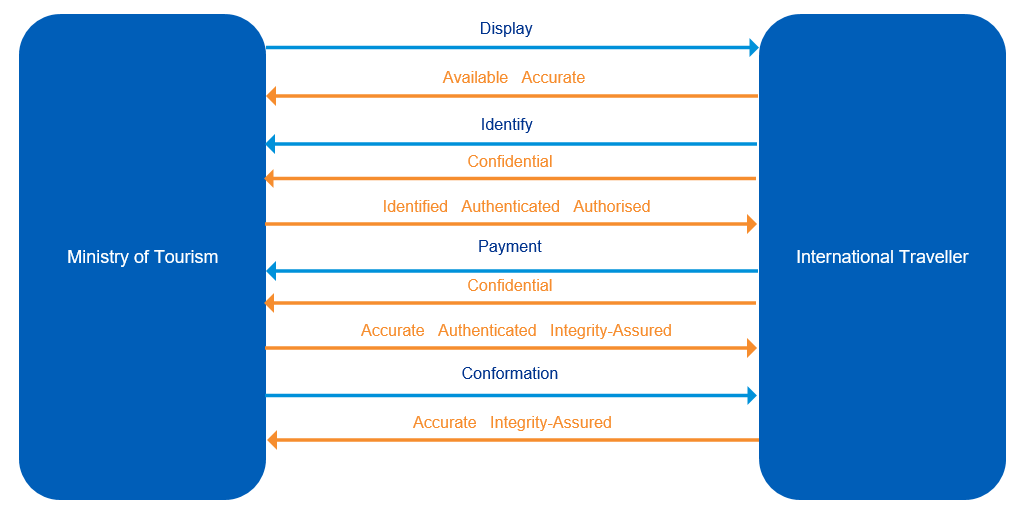
These are the exact attributes we identified as relevant for this transaction on the business process map above. It’s ok if you uncover additional security attributes at this stage. If that’s the case, feel free to add them retrospectively to your business process map at the Conceptual Architecture level.
Physical architecture
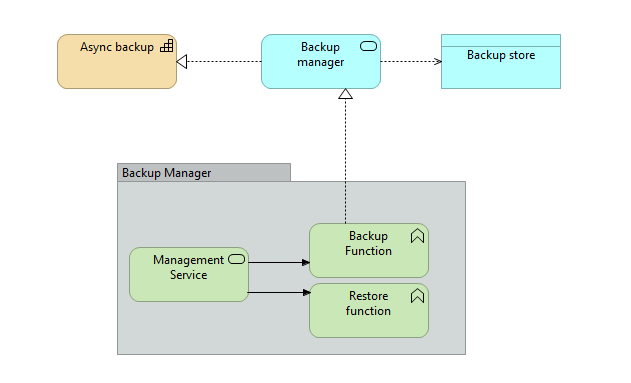
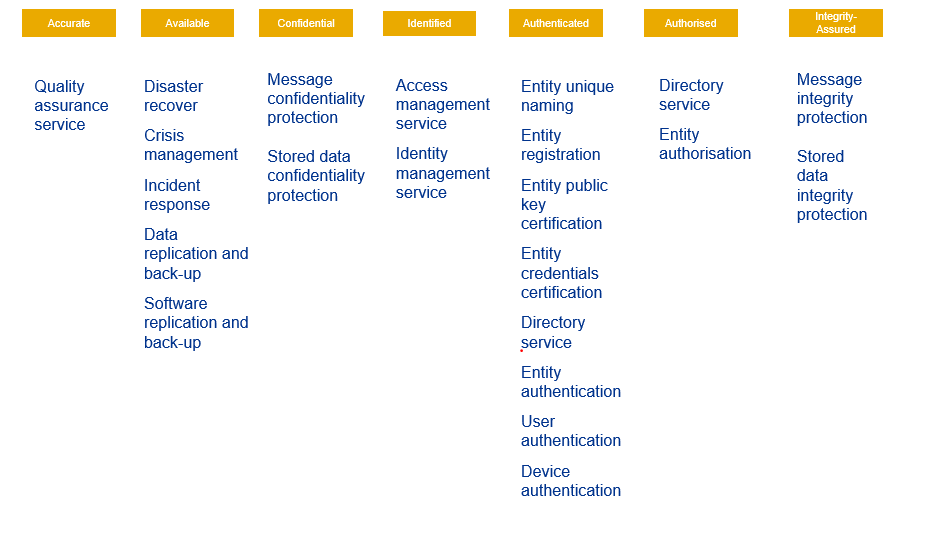
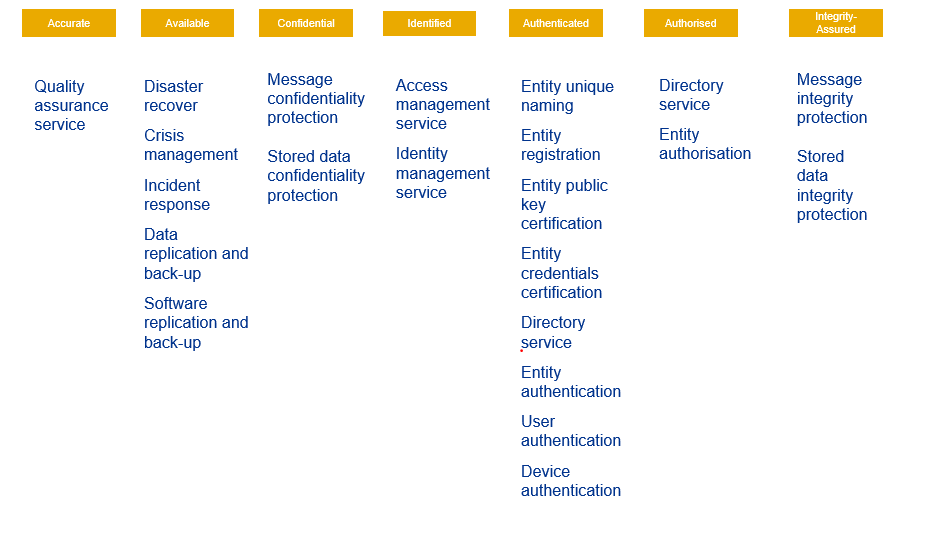
After the exercise above is completed for each interaction, it’s time to go down to the Physical Architecture level and define specific security services for each attribute for every transaction:
Component architecture
At the Component Architecture level, it’s important to define solution-specific mechanisms, components and activities for each security service above. Here is a simplified example for confidentiality and integrity protection for data at rest and in-transit:
| Service |
Physical mechanism |
Component brands, tools, products or technical standards |
Service Management activities required to manage the solution through-life |
| Message confidentiality protection |
Message encryption |
IPSec VPN |
Key management, Configuration Management, Change management |
| Stored data confidentiality protection |
Data encryption |
AES 256 Disk Encryption |
Key management, Configuration Management, Change management |
| Message integrity protection |
Checksum |
SHA 256 Hash |
Key management, Configuration Management, Change management |
| Stored data integrity protection |
Checksum |
SHA 256 Hash |
Key management, Configuration Management, Change management |
As you can see, every specific security mechanism and component is now directly and traceable linked to business requirements. And that’s one of the ways you demonstrate the value of security using the SABSA framework.