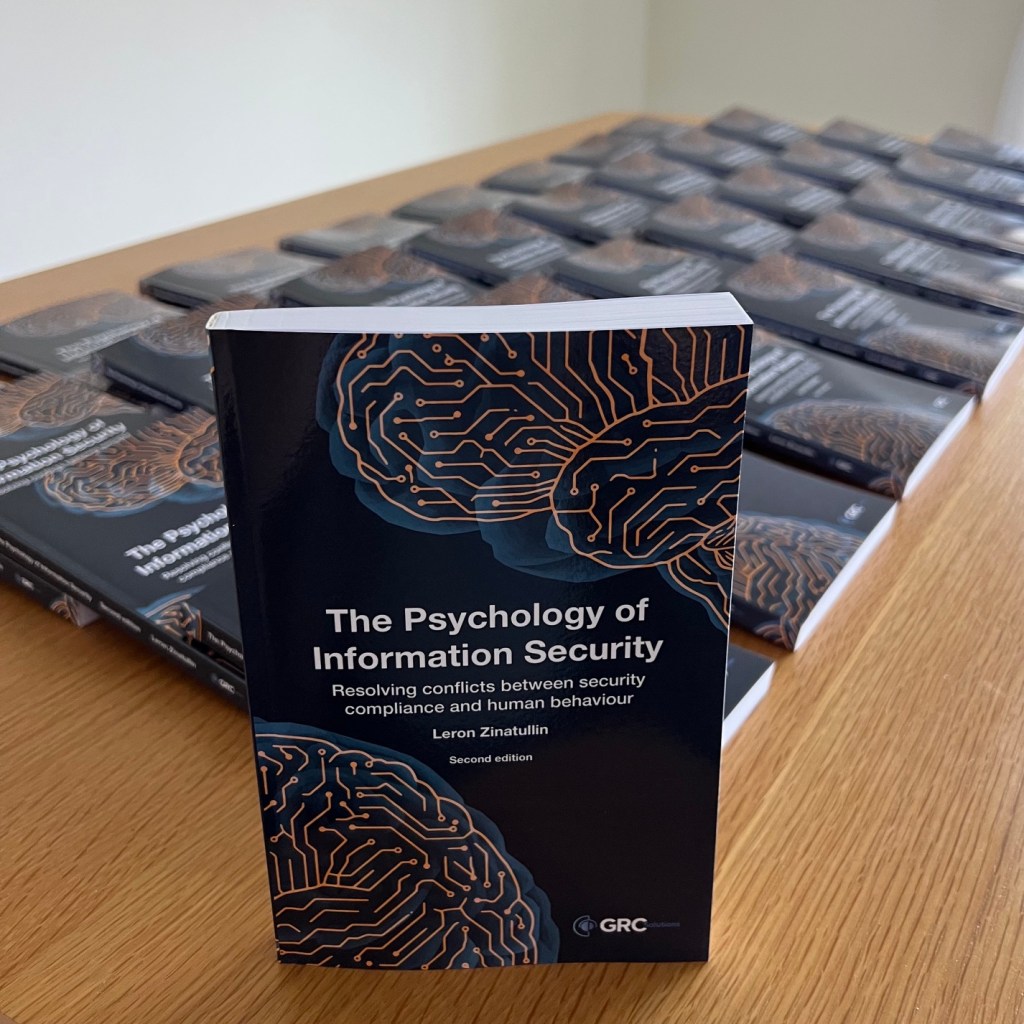
One of the UK’s leading research-intensive universities has selected the second edition of The Psychology of Information Security to be included in their flagship Information Security programme as part of their ongoing collaboration with industry professionals.
“We incorporated The Psychology of Information Security into our MSc in Information Security, where it has become part of the essential reading for the Human Aspects of Security and Privacy module. Over time, it has proven to be a valuable anchor text within the curriculum, helping to frame discussions around the human dimensions of cybersecurity in a structured and coherent way.
Students consistently appreciate the perspectives it offers, particularly its ability to bridge academic research with real-world industry practice. It not only provides a clear roadmap through a complex and wide-ranging topic, but also encourages a broad understanding of the psychological principles underpinning everyday security challenges.”
Dr Konstantinos Mersinas, PhD, CISSP
Associate Professor, Information Security Group, Royal Holloway, University of London
Visiting Professor, Keio University Tokyo, Japan 特別 招聘 准教授 慶応 大学 東京 日本
Director of Distance Learning MSc Programme in Information Security
Vice Chair, INCS-CoE (International Cyber Security Center of Excellence)