
Governments across Europe recognised that with increased interconnectiveness a cyber incident can affect multiple entities spanning across a number of countries. Moreover, impact and frequency of cyber attacks is at all-time high with recent examples including:
- 2017 WannaCry ransomware attack
- 2016 attacks on US water utilities
- 2015 attack on Ukraine’s electricity network
In order to manage cyber risk, the European Union introduced the Network and Information Systems (NIS) Directive which requires all Member States to protect their critical national infrastructure by implementing cyber security legislation.
Each Member State is required to set their own rules on financial penalties and must take the necessary measures to ensure that they are implemented. For example, in the UK fines, can be up to £17 million.
And yes, in case you are wondering, the UK government has confirmed that the Directive will apply irrespective of Brexit (the NIS Regulations come into effect before the UK leaves the EU).
Who does the NIS Directive apply to?
The law applies to:
- Operators of Essential Services that are established in the EU
- Digital Service Providers that offer services to persons within the EU
The sectors affected by the NIS Directive are:
- Water
- Health (hospitals, private clinics)
- Energy (gas, oil, electricity)
- Transport (rail, road, maritime, air)
- Digital infrastructure and service providers (e.g. DNS service providers)
- Financial Services (only in certain Member States e.g. Germany)
NIS Directive objectives
In the UK the NIS Regulations will be implemented in the form of outcome-focused principles rather than prescriptive rules.
National Cyber Security Centre (NCSC) is the UK single point of contact for the legislation. They published top level objectives with underlying security principles.
Objective A – Managing security risk
- A1. Governance
- A2. Risk management
- A3. Asset management
- A4. Supply chain
Objective B – Protecting against cyber attack
- B1. Service protection policies and processes
- B2. Identity and access control
- B3. Data security
- B4. System security
- B5. Resilient networks and systems
- B6. Staff awareness
Objective C – Detecting cyber security events
- C1. Security monitoring
- C2. Proactive security event discovery
Objective D – Minimising the impact of cyber security incidents
- D1. Response and recovery planning
- D2. Lessons learned
Table view of principles and related guidance is also available on the NCSC website.
Cyber Assessment Framework
The implementation of the NIS Directive can only be successful if Competent Authorities can adequately assess the cyber security of organisations is scope. To assist with this, NCSC developed the Cyber Assessment Framework (CAF).
The Framework is based on the 14 outcomes-based principles of the NIS Regulations outlined above. Adherence to each principle is determined based on how well associated outcomes are met. See below for an example:
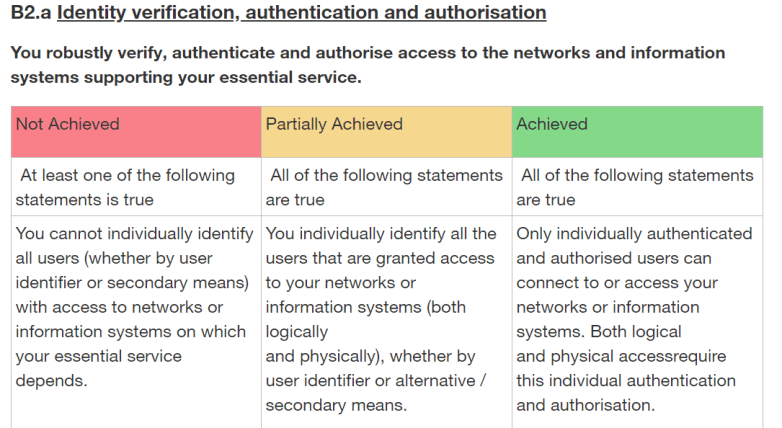
Each outcome is assessed based upon Indicators of Good Practice (IGPs), which are statements that can either be true or false for a particular organisation.
Whats’s next?
If your organisation is in the scope of the NIS Directive, it is useful to conduct an initial self-assessment using the CAF described above as an starting point of reference. Remember, formal self-assessment will be required by your Competent Authority, so it is better not to delay this crucial step.
Establishing an early dialogue with the Competent Authority is essential as this will not only help you establish the scope of the assessment (critical assets), but also allow you to receive additional guidance from them.
Initial self-assessment will most probably highlight some gaps. It is important to outline a plan to address these gaps and share it with your Competent Authority. Make sure you keep incident response in mind at all times. The process has to be well-defined to allow you report NIS-specific incidents to your Competent Authority within 72 hours.
Remediate the findings in the agreed time frames and monitor on-going compliance and potential changes in requirements, maintaining the dialogue with the Competent Authority.