Aligning OWASP Application Security Verification Standard and SABSA Architecture framework.
OWASP Application Security Verification Standard (Standard) is used at one of my clients to help develop and maintain secure applications. It has been used it as blueprint create a secure coding checklist specific to the organisation and applications used.
Below is an excerpt from the Standard related to the authentication verification requirements:
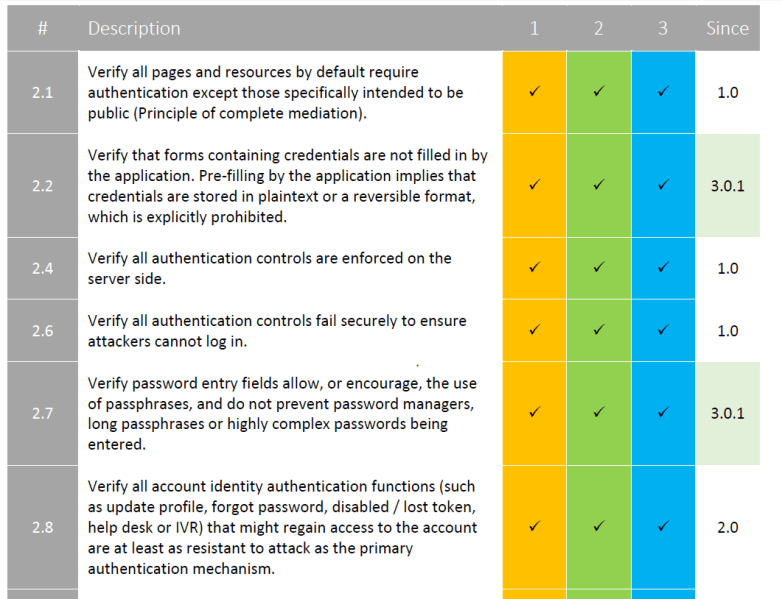
The Standard provides guidance on specific security requirements corresponding to the Physical layer of the SABSA architecture.
As there’s no clear link to the business requirements, let’s perform alignment between two frameworks.
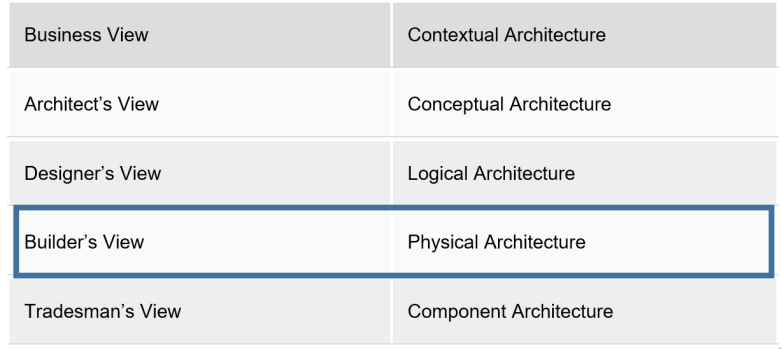
The first step is to gain an understanding of Contextual and Conceptual architectures.
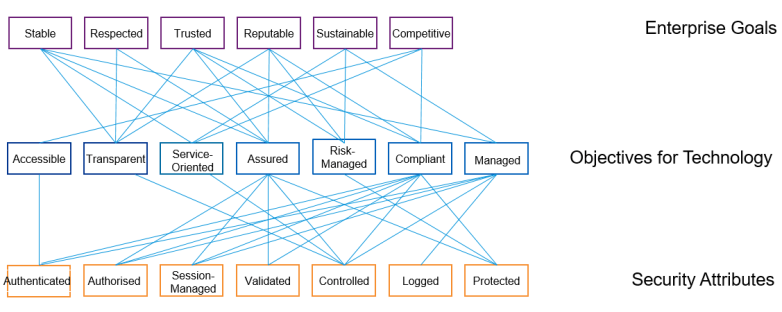
From analysing the company’s corporate strategy I was able to derive multiple business attributes relevant to the shareholders:
After a workshop with the CIO and IT managers in various business units, I’ve defined the following IT attributes supporting the main business attributes and the relationships between them:

How does the security function support the wider IT objectives and corresponding attributes? After a number of workshops and analysis of the security strategy document I’ve created a number of security attributes. Below is an example correlating to the business and IT attributes in scope:
The next step is to develop the security attribute mapping to the requirements of an in-house application security policy, based on the OWASP Application Security Verification Standard:
| Requirement | Requirement Description |
| Authenticated | |
| A1 | Application must use established corporate directory services for authentication i.e. LDAP. |
| A2 | Authentication must be performed over a secure connection like SSL/TLS to avoid data sniffing. |
| A3 | Authentication mechanism must not store sensitive credentials on the client. |
| A4 | Authentication credentials must not be submitted using URL parameters to avoid sniffing. |
| A5 | Authentication failure response must never indicate which part of the authentication data was incorrect to prevent username enumeration. |
| A6 | Password entry fields must enforce a combination of upper-case, lower-case, special-chars, numbers and a minimum length for secure password. |
| A7 | All authentication controls must be enforced on the server side because it’s easy to tamper with data on the client side. |
| A8 | Authentication credentials must be salted and stored using industry defined and proven hashing techniques. |
| A9 | Forgot password and other recovery paths must send a link including a time-limited activation instead of the password itself. |
| A10 | There must be no secret question and answer mechanism for resetting the password to thwart social engineering attacks. |
| A11 | Forget password functionality must not disable the login for valid users to ensure valid users don’t get locket out. |
| A12 | Authentication mechanism must define the account lockout policy in case of 3 to 5 wrong login attempts to avoid brute-force attacks. |
| Authorised | |
| B1 | Access Control process must be defined, agreed upon, and effectively implemented. The process must cover user authorization management, roles and responsibilities, and access revocation and expiry. |
| B2 | The authorization business roles must be defined and documented. |
| B3 | Authorization controls must be designed using the Principle of Least Privilege i.e. a user should not be granted excess privileges which is not required to perform his job. |
| B4 | Business roles must never have authorization to perform application administration functions. |
| B5 | An application must utilize a central component for authorization. |
| B6 | Only trusted system objects must be used for making authorization decisions. |
| B7 | Authorization check must be performed at every entry point of an application. |
| B8 | Authorization controls must fail securely; all access must be denied if the application cannot access its security configuration information. |
| Managed | |
| C1 | The application must use the session management mechanism provided by the framework or server instead of a custom solution. Session management provided by the framework or server is thoroughly tested for security and hence safe to use. |
| C2 | Session creation and management must be done on a trusted system and never on the client side. |
| C3 | A new session must be established upon log-in and re-authentication to prevent session-fixation attacks. |
| C4 | User must be forced to re-authenticate when attempting to access a function that requires elevated privileges. |
| C5 | An idle session timeout and an absolute session timeout regardless of activity must be set. |
| C6 | The logout function must explicitly terminate the user session and destroy all session related data. |
| C7 | Session ids must have high entropy to avoid session id guessing attacks. |
| C8 | The Session ID is sensitive; it must be protected and never displayed except in cookie headers. |
| C9 | Session ID cookies must be marked as HttpOnly to avoid an XSS flaw from gaining access to it. |
| C10 | User provided session ids must never be accepted. |
| C11 | Concurrent session for the same user must not be allowed. |
| Validated | |
| D1 | All user-input coming from drop-down, text fields, value lists, and other UI components must be validated. By default the user input should be considered malicious. |
| D2 | Special characters in input like (but not limited to) <, >, &, ’” if used in the output must be html escaped to make them context safe. |
| D3 | Input validation and encoding must be performed on the server side. |
| D4 | Queries passed to SQL databases must be parameterized or stored procedures should be used to prevent SQL injection attacks. |
| D5 | All input validation failures must be logged to detect attack if any. |
| D6 | Input validation failure message should not display any system or configuration information to the user. It may assist the attacker in profiling the system. |
| D7 | Input validation failures must result in input rejection. |
| D8 | File upload functions must be implemented securely. Uploaded file should be checked for virus and other malicious data |
| Controlled | |
| E1 | Error messages must not display any technical information about the application or the underlying infrastructure to thwart any attempt to profile the system. |
| E2 | Application design must perform proper exception handling and must not solely rely on the underlying framework or infrastructure for handling errors. |
| E3 | System resources that are no longer needed upon occurrence of an exception must be explicitly released. |
| E4 | Application design must deny access by default. |
| Logged | |
| F1 | Logging controls must be implemented on a trusted system. |
| F2 | Access to logs must be strictly controlled. |
| F3 | Sensitive information must not be stored in system logs. |
| F4 | Successful and unsuccessful login attempts must be logged. |
| F5 | Attempts to access unauthorized sensitive transactions must be logged. |
| F6 | Sensitive transactions and administrative actions must be identified and their usage logged. |
| F7 | Unexpected application exceptions must be logged. |
| F8 | Centralized monitoring of logs must be setup for critical applications. |
| F9 | A log retention, access, and review process must be defined and effectively implemented. |
| Protected | |
| G1 | All sensitive data consumed and produced by an application must be classified and there should be a clear policy for access control to these data. |
| G2 | The retention period must be obtained or determined for any data stored by an application. |
| G3 | All sensitive information must be transmitted using the latest version of SSL/TLS. |
| G4 | Only industry accepted encryption/hashing algorithms must be used. Outdated and weak hashing algorithm like MD5 should never be used. |
| G5 | Data at rest must be protected by means of access control, and where required, by encryption |
| G6 | Sensitive information must not be transmitted in GET query string or in URL parameter. |
| G7 | User credentials must never be hard-coded or stored in config/plaintext files. |
| G8 | An application must not reveal technical information about system components or underlying infrastructure. |
| G9 | Unnecessary application code, documentation and components must be removed before deployment to production environment. |
| G10 | Cookies sent over HTTPS must be marked as secure. |
| G11 | Extranet applications must protect against Clickjacking attack by setting the iframe as same-origin in the cookie. |
| G12 | Client side caching should be disabled for sensitive information using appropriate header or meta-tag like no-cache, Cache-Control, no-store. |
| G13 | Temporary data or files must be invalidated after session termination. |
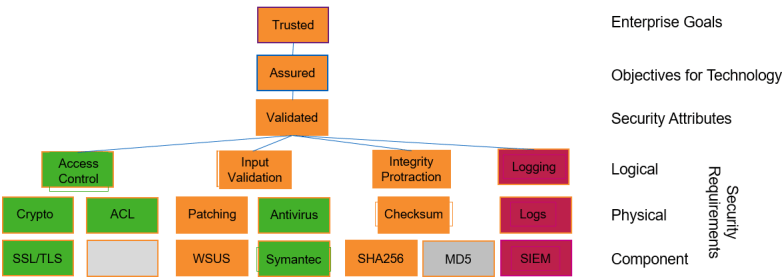
Further aligning the application security policy to the SABSA framework, let’s invent the link between the SABSA layers, developing Logical, Physical and Component architectures:

Note that the list of security requirements and control objectives is not exhaustive and presented for illustrative purposes only.
The Standard defines three security verification levels, with each level increasing in depth. Each ASVS level contains a list of security requirements. Each of these requirements can also be mapped to security-specific features and capabilities that must be built into software by developers.
Let’s map risk level for every security attribute and corresponding components to the Standard verification levels:

The combined framework can now be used for high-level risk reporting:
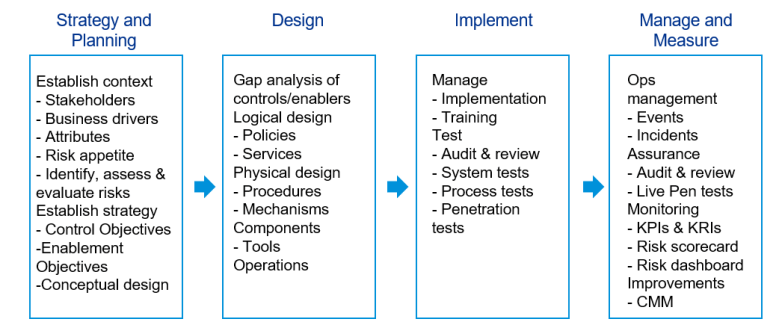
The OWASP framework is designed as a set of requirements to measure point-in-time compliance with the Standard. I propose widening the scope of the framework to include activities I performed above as part of the following lifecycle:
Controls and control objectives are clearly defined in the Standard in order to address the risks, yet the focus on enablers to exploit potential opportunities is lacking. Below is an example of how a balanced approach might look like for the attribute Authenticated.
| Attribute | Enablement Objectives | Control Objectives |
| Authenticated | 1. Ensure that all essential enterprise information uses centralized authentication and access control mechanisms.
2. Encourage information creators and users to leverage centralized content repositories for all information essential to performing their day-to-day activities. 3. Where possible, use automatic assignment of information and data ownership and permissions to ensure information elements are accessed by only those individuals who have a legitimate business need. 4. Where possible, do not require users to explicitly manage individual access control permissions and authorizations. |
Ensure that a verified application satisfies the following high level requirements:
1. Verifies the digital identity of the sender of a communication. 2. Ensures that only those authorised are able to authenticate and credentials are transported in a secure manner.
|
There is also a lack of metrics and performance targets in the OWASP Standard. To address this, I’ve developed a set of metrics and measurement approaches for security attributes with corresponding primary and secondary risk indicators. Below is an example for the attribute Authenticated.
| Attribute | Metric | Measurement Approach | Category | Primary KRI | Secondary KRI |
| Authenticated | % of information elements stored in repositories, locations or on devices requiring authentication of some kind before the information can be accessed | Audit of information repositories and storage locations.
|
Completeness | 80% | 90% |
| Authenticated | % of applications using established corporate directory services for authentication | Audit of web applications | Completeness | 80% | 90% |
| Authenticated | % of applications performing authentication over SSL/TLS | Audit of web applications | Completeness | 80% | 90% |
| Authenticated | % of applications storing authentication credentials on the client. | Audit of web applications | Completeness | 80% | 90% |
| Authenticated | % of applications enforcing password requirements | Audit of web applications | Completeness | 80% | 90% |
How do you demonstrate benefits of the combined framework to the stakeholders?
The following stakeholders have been chosen to demonstrate features, advantages and benefits of the combined OWASP-SABSA framework as they are directly impacted by this change:
- Chief Executive Officer (CEO) and the Board of Directors
- Chief Risk Officer (CRO)
- Chief Information Officer (CIO)
- Chief Information Security Officer (CISO)
The table below provides a summary of benefits of the aligned framework.
| Feature | Advantage | Benefit | |||
| CEO and Board | CRO | CIO | CISO | ||
| Business-driven | Value-assured | Protects corporate reputation and | Enables flexible fit with industry regulations | Enables secure adoption of digital business model | Facilitates alignment of application security efforts with business goals |
| Transparent | Two-way traceability | Ensures return on investment | Enables effective compliance measurement approach | Encourages integrated people – process – technology solutions | Provides traceability of implementation of business-aligned security requirements |
| Auditable | Demonstrates compliance to relevant authorities | Demonstrates compliance to regulators and external auditors | Ensures that compliance risk is effectively managed | Facilitates effective internal information systems audits | Supports application security and risk review processes |
References: