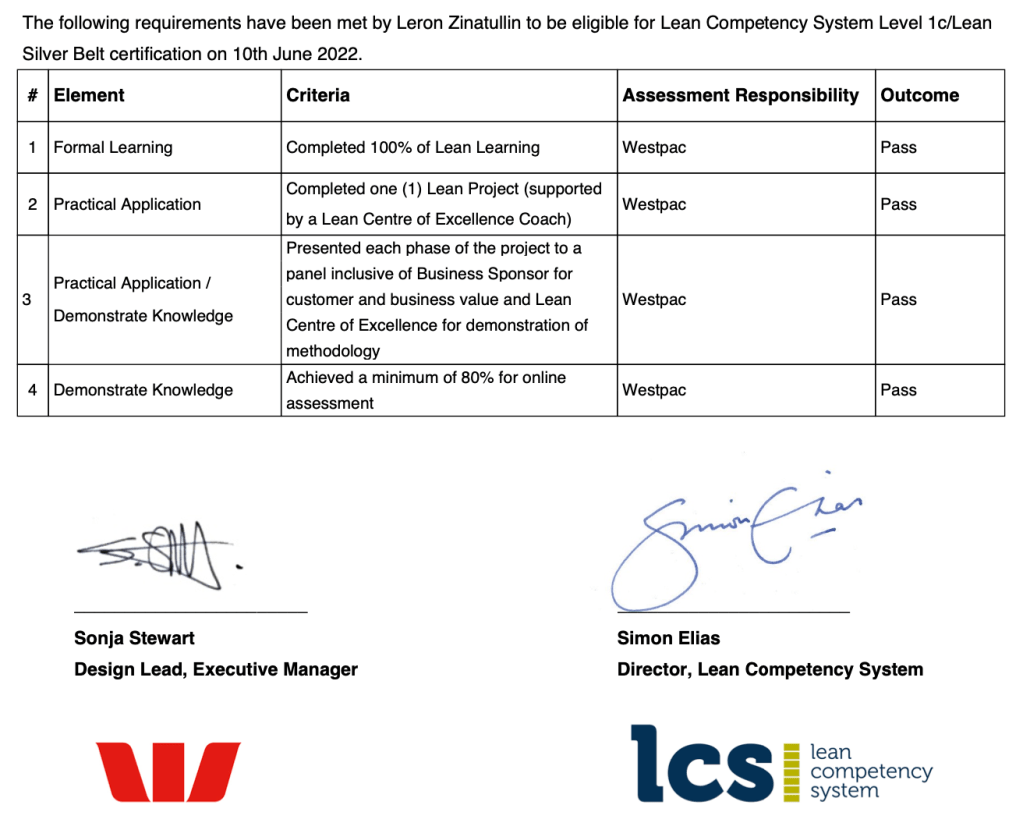
I had an opportunity to follow the Lean Silver Belt pathway of Cardiff University’s Lean Competency System and work with a coach to deliver measurable business process improvement in the workplace. This resulted in significant cost savings for the business and was supported by the official accreditation.
A lot of it is to do with the mindset: spotting inefficiencies, eliminating waste and continuous improvement are at the core of the approach. It’s also about applying these concepts and techniques to real world challenges.
The journey is very collaborative in nature and I had a chance to work with stakeholders from different parts of the business to define a problem statement, come up with an initial hypothesis, identify the attributes and metrics that are critical to quality and start gathering the data. None of it is rocket science but consistent application of proven techniques helps clarify the assumptions and get everyone on the same page.
One of such techniques is SIPOC. It’s an acronym made up of the first letters of elements that make up a high-level process map: Suppliers, Inputs, Processes, Outputs, and Customers. Gaining visibility and clarity about the process in scope is key. All too often this is the first time people ask who this process serves and how. Creating customer personas and journeys can deepen your understanding.
One of the most insightful techniques for me personally is Value Stream Mapping (VSM). I facilitated a number of workshops with subject matter experts to map the current process and to identify pain points and waste. Having the customer in mind during the discussion and challenging stakeholders can help elicit value adding and non-value adding activities and gather metrics like processing time, waiting time and accuracy.
Once barriers to flow have been identified for the current process, a future state can be developed and countermeasures proposed to address the pain points. Root cause analysis and 5 Whys are useful techniques to get to the bottom of the issue rather than merely treating the symptoms of the problem.
Initiatives are then prioritised to get to the target state based on the impact to customer and ease of implementation. Here quick wins often become obvious and can be addressed straight away. Stakeholders are kept engaged in line with the communication plan and charters for each initiative.
Benefits of the process improvement can be quantified financially too. We know how many people are involved in the current process, how long it takes them and averaging their salary against the processing and wait time across each step of the process makes it very clear how much this inefficiency is costing the organisation every year. This can be compared to the future state estimates also discussed during the VSM workshop.
A number of initiatives can then be launched to improve the process and achieve the proposed future state. This is followed by post implementation review that includes lessons learnt. Senior stakeholders in the business have a chance to share their feedback and continue prioritising other improvement opportunities.
All this has direct application to cyber security: knowing who your customer is and supporting the business through improving processes not only saves money but also elevates the security team’s brand. Taking steps to eliminate waste can also reduce unnecessary friction that too many security teams are perceived to create for the organisation. It demonstrates the business acumen and awareness of objectives related to cost performance that helps position the security function as an enabler.