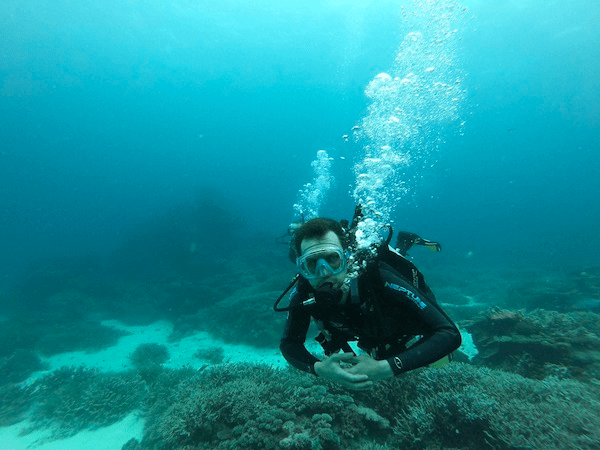
During one of my dives I pondered if there are any parallels we can draw between scuba diving and cyber security. They may seem like vastly different activities, but they share many important similarities. Both are dealing with unknown and often rapidly changing environments, where careful preparation, attention to detail and a focus are critical for success. I list some themes in this blog, feel free leave a comment to add your own.
1. Risk management.
Both scuba diving and cyber security involve managing risk. In scuba diving, divers must manage the risk of running out of air, getting lost, or encountering dangerous currents. In cyber security, risks of data breaches, service outage and regulatory fines should be assessed and mitigated. In both cases, however, the reward of being able to explore the ocean and launch new products are there, so it helps to remember that although risks may look daunting, a balanced approach can enable you and your organisation to operate safely and securely.
2. Teamwork
In both scuba diving and cyber security teamwork is key. In scuba diving, a buddy system is often used to ensure that each diver has someone looking out for them. Similarly, in cyber security, people must work together to identify and respond to threats to be effective. You cannot do it alone.
3. Preparation and planning
Scuba divers are trained to use specialised equipment and go through rigorous training on safety procedures. In the same way, learning cyber security principles is key to being successful. Just like a diver checking and testing their air tanks and diving equipment before entering the water, cyber security professionals follow standard operating procedures to make sure security controls are operating effectively.
A successful scuba dive requires careful planning. A dive plan must be created that takes into account factors such as depth, currents, and dive time. In cyber security, incident response planning is also crucial. People must be clear on their roles during a potential cyber attack and incident response plans should be tested regularly.
4. Monitoring and response
Once a scuba diver enters the water, they must be aware of their surroundings at all times, constantly monitoring their air supply and being mindful of underwater currents and marine life. In much the same way, cyber security professionals must constantly monitor their networks and systems for signs of intrusion or attack, like a diver scanning the underwater environment for potential hazards.
When the unexpected occurs, quick thinking and a calm demeanour are essential in both scuba diving and cyber security. Just as a scuba diver must react quickly and remain composed in the face of a sudden change in water conditions, a cyber security professional must also remain vigilant and composed in the face of a potential cyber attack. This requires problem-solving skills, just like a diver having to handle an equipment malfunction, calmly and effectively, to ensure a safe dive.
I remember the instructor’s advice during my open water diving course – in an emergency, stop, breathe, think and then act. It helps break the automatic emotional response and execute a logical plan based on your training.
5. Continuous learning
There’s need for continued education and improvement. Both scuba diving and cyber security are constantly evolving, with new approaches and technologies being developed all the time. A scuba diver must keep up to date with the latest diving equipment and best practices, while cyber security professionals must stay informed about evolving cyber threats and countermeasures.
Whether you are exploring the depths of the ocean or protecting your organisation from cyber threats, these principles will help you to stay safe and secure. Don’t forget to have some fun!