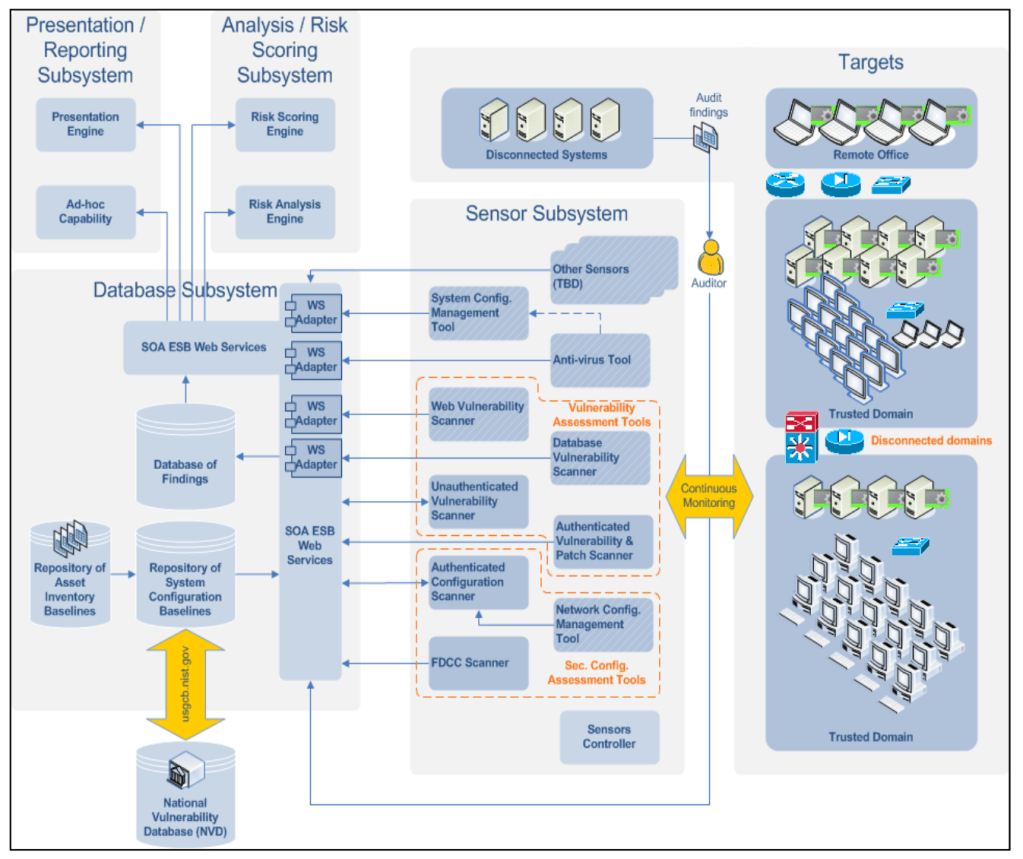
Today, organisations are caught between two opposing forces. On one side is the drive for operational efficiency through digital transformation and AI adoption. On the other is an asymmetric cyber threat landscape.
As adversaries leverage AI to increase the scale and sophistication of attacks overwhelming already stretched cyber teams, defenders must do the same by using AI to strengthen security.
The traditional security model is reactive. When a threat is detected, a human must review, validate and remediate. In the time it takes an analyst to finish their first coffee, an AI-driven adversary can exfiltrate sensitive data.
For organisations that depend on customer trust and regulatory compliance, “responding as fast as we can” is no longer within risk appetite. Humans cannot scale to match the speed of automated code.
AI is becoming central to the future of cyber defence. While much of the industry focuses on automating security operations triage, the true power of AI lies in automating complex, proactive security and compliance functions that previously required thousands of human hours.