
‘You won’t see it all’ – that’s what I was told before I headed out to the RSA Conference for the first time! With so many great talks, side events, meetings, vendor showcases people will have very different impressions of this event. Here are mine.
A practical approach


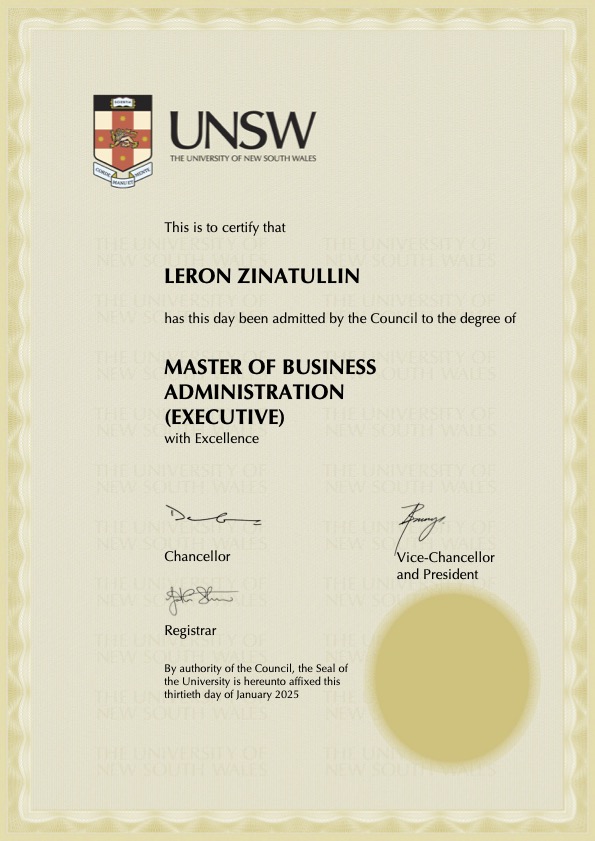
I’m excited to share that I have graduated with Excellence from the Executive MBA program at AGSM UNSW Business School. This transformative 2-year journey has been as challenging as it has been rewarding, redefining my approach to strategy, leadership and execution.
Throughout the program, I had an incredible opportunity to bring theory into practice – collaborating with a diverse cohort of leaders to work on real-world challenges across Australian industries such as technology, manufacturing, financial services and retail. These experiences not only honed my analytical skills but also deepened my appreciation for applying business concepts in evolving fields like cybersecurity and AI.
A pivotal part of my journey was the capstone strategic consulting project with First Nations organisations. This experience reshaped my perspective on culture and inclusivity.
The international exchanges were equally transformative. Spending time in Shanghai at Fudan University and completing a semester at Yale School of Management allowed me to engage with global leaders, enhancing my understanding of cross-cultural leadership. The practical case studies and strategic projects I completed in these environments reinforced the significance of a global mindset in today’s interconnected world.
I also had an opportunity to focus on social impact and the for-purpose sector in collaboration with the Centre for Social Impact and received the Professor Wanbil Lee Prize for Ethical Leadership and the Responsible Management Prize for my work.
With courses ranging from accounting and marketing to negotiations, I am grateful for every lesson learnt, every challenge overcome and every connection made along the way. I look forward to leveraging these insights to drive innovation, inspire ethical leadership and create meaningful impact.

I really enjoyed the cyber risk quantification workshop led by Richard Seiersen, co-author of How to Measure Anything in Cybersecurity Risk.
During the session, Richard broke down risk quantification, focusing on identifying the risks most likely to cause significant business losses where assets, threats and vulnerabilities intersect.
I’m also glad to receive his book for correctly estimating cost in our the discussions. It’s one of the most influential books in security: it challenges subjective risk assessments, offering practical frameworks for using data, probability and economics to drive smarter security decisions.

I had the privilege of joining a panel discussion on the rapidly evolving regulatory landscape and its impact on businesses worldwide. With cyber threats, operational disruptions, and AI risks on the rise, governments are strengthening regulations to drive security, resilience and accountability across industries.
In Europe, major frameworks like DORA (Digital Operational Resilience Act), NIS2 (Network and Information Security Directive) and the EU AI Act are reshaping how organisations approach cybersecurity, operational resilience, and responsible AI governance. But this shift isn’t limited to the EU – regulatory scrutiny is increasing globally, from the U.S. to APAC, with frameworks reinforcing risk management, third-party oversight and AI transparency.
A huge thank you to my fellow panelists and engaged audience members for an insightful discussion.

Cyber security is a relentless race to keep pace with evolving threats, where staying ahead isn’t always possible. Advancing cyber maturity demands more than just reactive measures—it requires proactive strategies, cultural alignment, and a deep understanding of emerging risks.
I had an opportunity to share my thoughts on staying informed about threats, defining cyber maturity, and aligning security metrics with business goals with Corinium’s Maddie Abe ahead of my appearance as a speaker at the upcoming CISO Sydney next month.



I had the privilege to join a brilliant cohort of CISOs at the RSA Conference CISO Bootcamp. It was an energising experience, where seasoned experts and emerging leaders in cybersecurity came together to tackle our industry’s most pressing challenges.
The bootcamp was more than just a learning experience; it was a platform for sharing personal insights, gaining fresh perspectives and engaging in a thought-provoking debate.
From discussing emerging threats to exchanging strategies for resilience, it was a reminder of the power of community in cybersecurity. A huge thanks to all organisers and speakers for creating a space where we can grow together and tackle our industry’s biggest challenges.






I just spent an incredible week immersed in Aboriginal culture, where I had the privilege of working shoulder to shoulder with First Nations organisations as part of my AGSM Executive MBA journey.
This experiential learning project allowed me to take the academic knowledge from all my previous MBA courses and apply it in real-world contexts. What a great way to wrap up the program!
It was also an opportunity to deliver the final client presentation to Indigiearth, a 100% Aboriginal-owned native foods business, concluding the capstone strategic consulting engagement we’ve been working on this term.
Learning directly from Elders and community members enriched my understanding of Aboriginal traditions, values and the profound connection to land that underpins Indigenous enterprises. I’m proud to have been a part of this journey, bringing together cultural respect and strategic vision.
In cybersecurity, collaboration is essential. With growing complexity in the threat landscape, leaders often find themselves working with parties they may not fully align with—whether internal teams, external stakeholders, or even rival firms.
Adam Kahane’s book Collaborating with the Enemy: How to Work with People You Don’t Agree with or Like or Trust outlines principles for collaborating effectively, especially in challenging environments where trust and agreement are minimal. Kahane’s “stretch collaboration” approach can transform the way cybersecurity leaders address conflicts and turn rivals into partners to meet critical security goals. In this blog, I’ll share my key takeaways.