I previously wrote about how to prepare for the Certified Cloud Security Professional (CCSP) and AWS Certified Solutions Architect – Associate exams. Today, I would like to focus on AWS Security – Specialty.
Exam cost aside, preparing for this specialty can be rather expensive. There is a whole industry around mock practice tests, study books, video tutorials and hands-on labs. Here I’ll aim to outline how to maximise the benefit while minimising costs, focusing on free resources.
Whitepapers, user guides and service FAQs
AWS documentation is arguably the best source of study material out there. I don’t know a single person who passed the exam without reading through at least some of them. Check out the official exam guide for the overview of domains to select the relevant ones. I focused on IAM, KMS, CloudTail, CloudWatch, VPC, Lambda, Inspector, GuardDuty, Athena, Macie and AWS Microsoft AD. At a very minimum, you should read these:
I also wrote about my experience in using security-related AWS services in my blog.
Online courses
Who needs paid for online tutorials when the AWS YouTube channel has a lot of their re:Invent talks available for free? There is literally a video on pretty much every subject you are interested in. There are too many to mention and you could conduct a simple search to find the latest talk on what you want, but I’ll recommend a few to get you started:
If you would rather have a structured online course instead and don’t mind paying a little bit for it, I recommend the Linux Academy and/or A Cloud Guru. I’ve done them both. Personally, I preferred the former as it had some hands-on labs, but A Cloud Guru is shorter and has some good exam tips. Besides, you can try both of them for free for 7 days and decide for yourself.
There is also the official AWS Exam Readiness: AWS Certified Security – Specialty course. It covers the exam structure, gives you tips on tackling questions and provides thorough explanations. I would save this one for last to get a view of your preparedness.
Practice tests
The obvious thing to do is to buy the official practice exam from AWS, right? Well, maybe not. Unless you’ve got it for free for passing one of the other AWS exams previously, you might be better off finding an alternative. It only includes 20 questions (which works out at $2 per question plus tax), and you don’t get to see the answers! Instead, you are presented with a pass/fail summary that gives you the overall percentage broken down by exam domains. You might be better off using the free 15 questions from Whizlabs, although I can’t recommend their paid products. Practice tests are also included in the Linux Academy and A Cloud Guru courses I mentioned above. Plus, the free official Exam Readiness course also comes with 24 questions with answers and explanations at the end. That should be enough to give you the feel for types of question on the exam.
Getting ready
When revising, I found some good notes and a mindmap from other students on the internet. You can also go through a set of flashcards (e.g. on Quizlet) to recap on what you’ve learned.
With all this preparation, don’t lose track of why you are doing it in the first place: gaining the skills that you can apply in practice. The exam gives a good indication of your weaker areas and encourages you to fill these gaps. The best way to do this is, of course, through hands-on experience. If your organisation relies on AWS, find ways to apply the newly acquired knowledge there to make your cloud infrastructure more secure. If that’s not an option, there is always the Free Tier, where you can put your skills into practice. Finally, the Linux Academy (and some other providers) for a small cost offer you some hands-on labs and even a whole sandboxed playground for you to experiment in.
AWS constantly evolve and refine their services, and add new ones too. Keep this in mind while studying, as things move pretty fast in the cloud world. This also means that your learning is never finished, even if you pass the exam. But I think this is a good thing and I’m sure you agree!





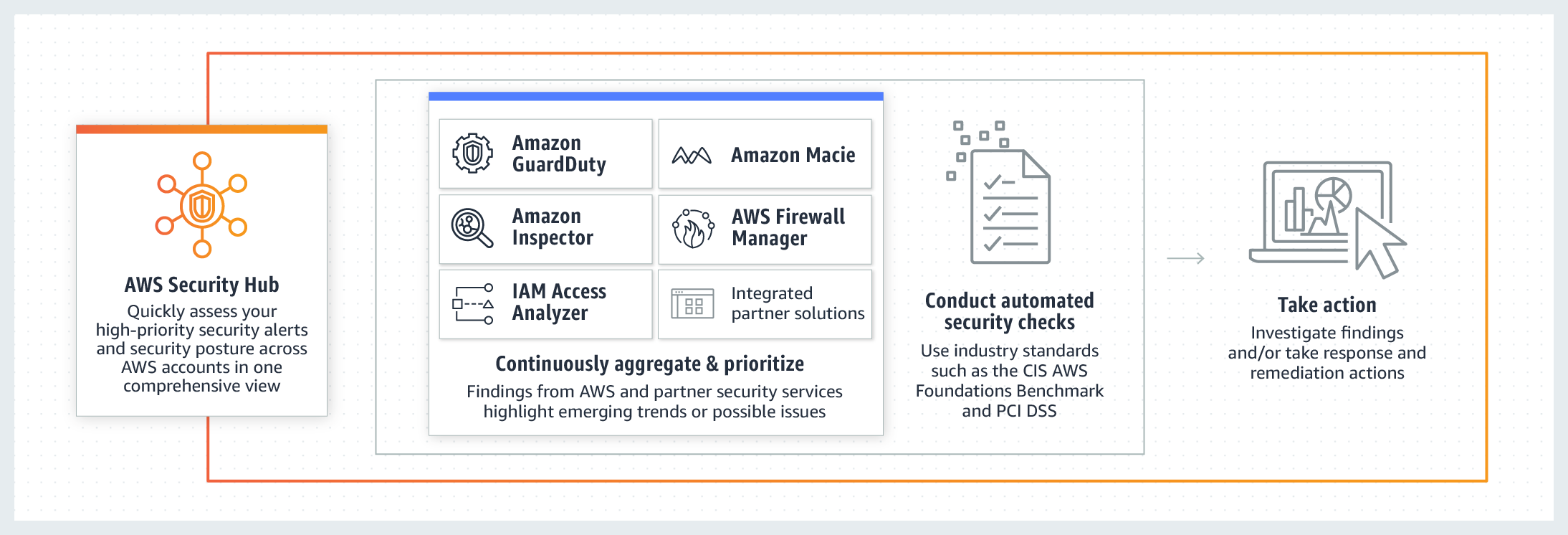
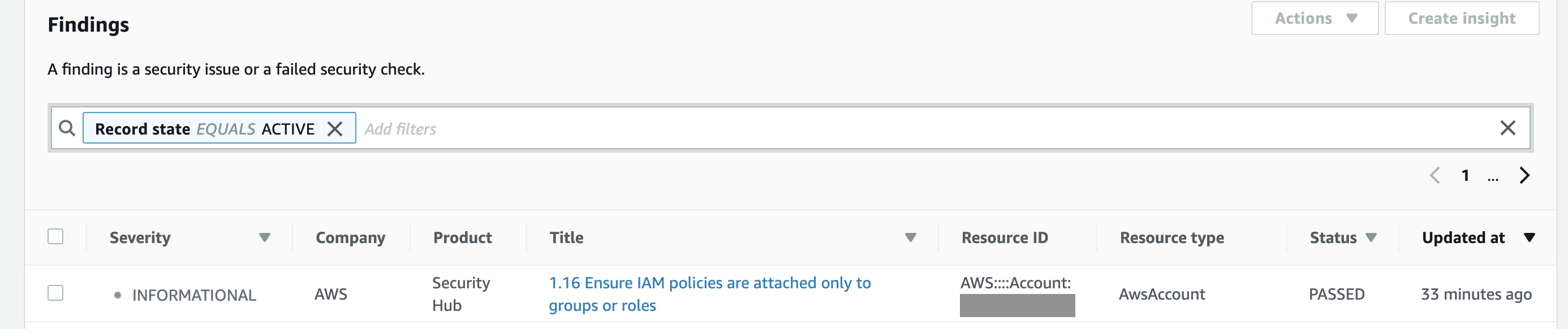


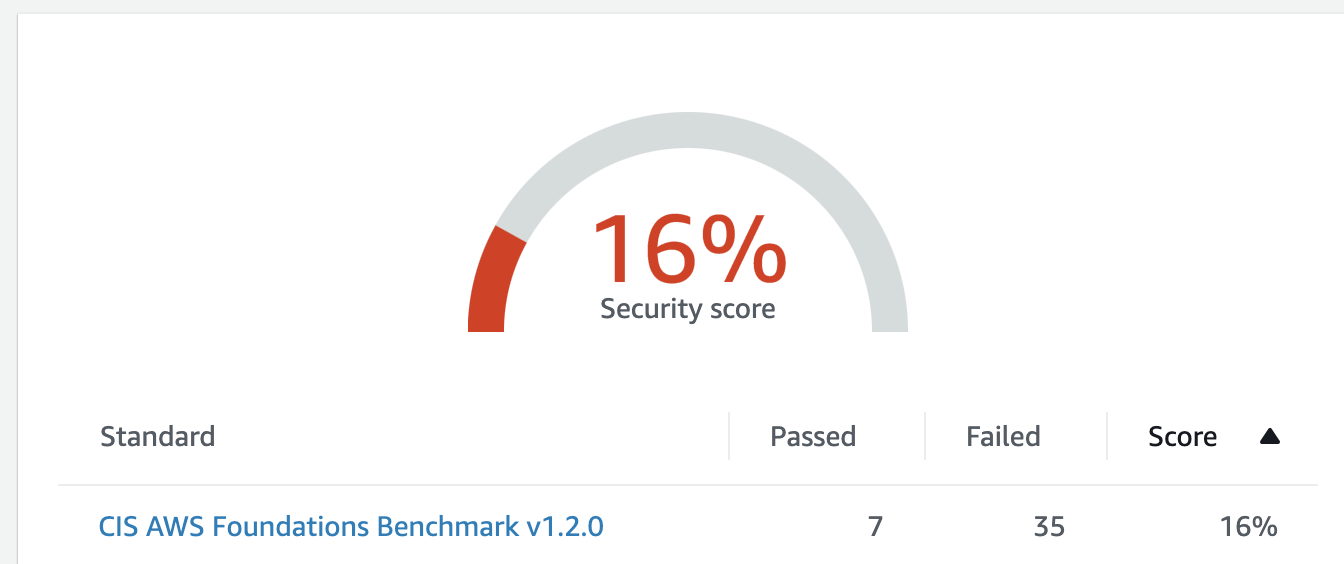
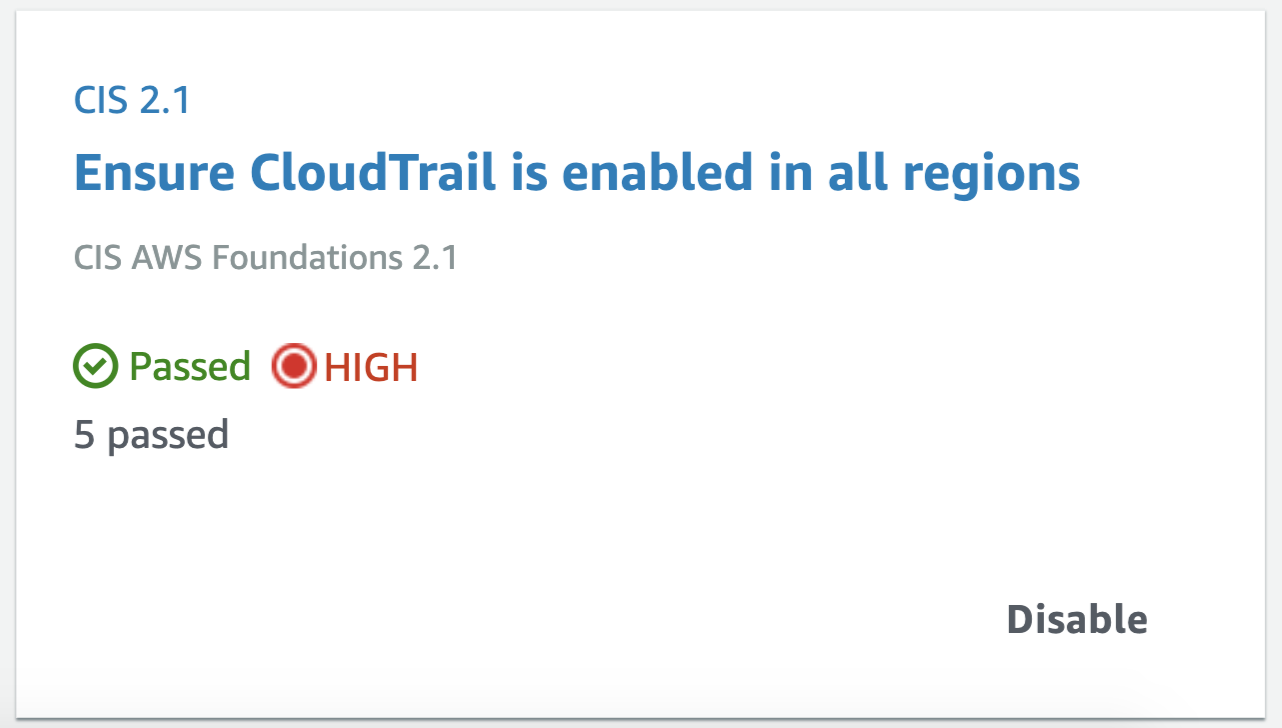 Apart from consolidating findings from other services, it also assesses your overall AWS configuration against PCI DSS and/or the
Apart from consolidating findings from other services, it also assesses your overall AWS configuration against PCI DSS and/or the