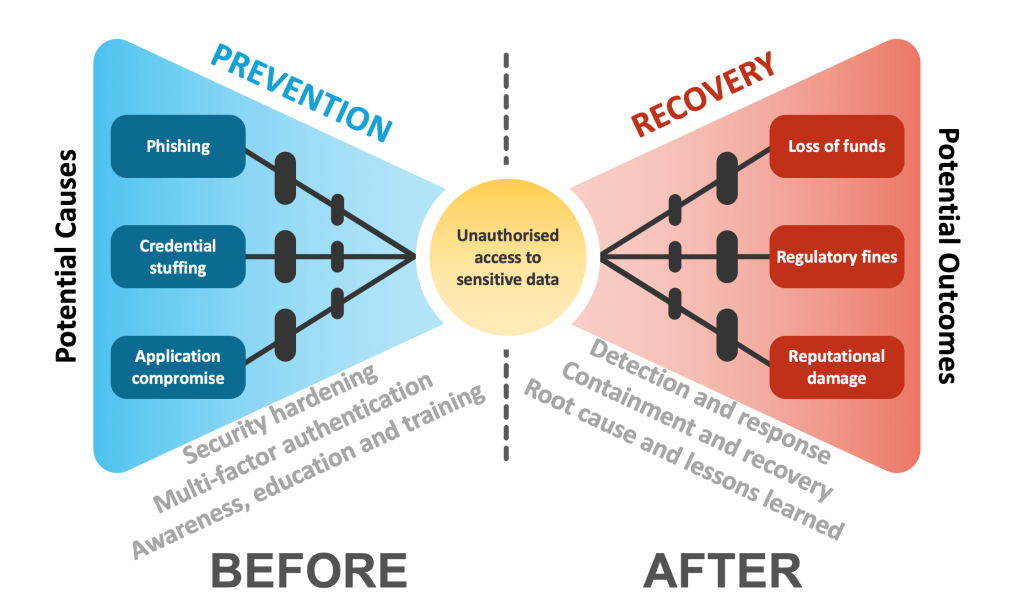
The focus of many of my projects is on risks. I’ve observed through multiple assessments in various companies and industries a lack of formalised risk management process. Some of the plans may exist but they are not linked to specific risks and risk reduction levels are not being measured and reported on appropriately.
The security function can be effective in responding to incidents but the strategic risk-driven planning is often missing. The root cause of this state of affairs is often can be generalised as low maturity of the security function. If that’s the case, the team spends most of its time fighting fires and have little capacity to address the challenges that cause these fires in the first place.
To address this, I assess current state of the security function, define the target maturity level and then develop a high-level roadmap to achieve that desired state.
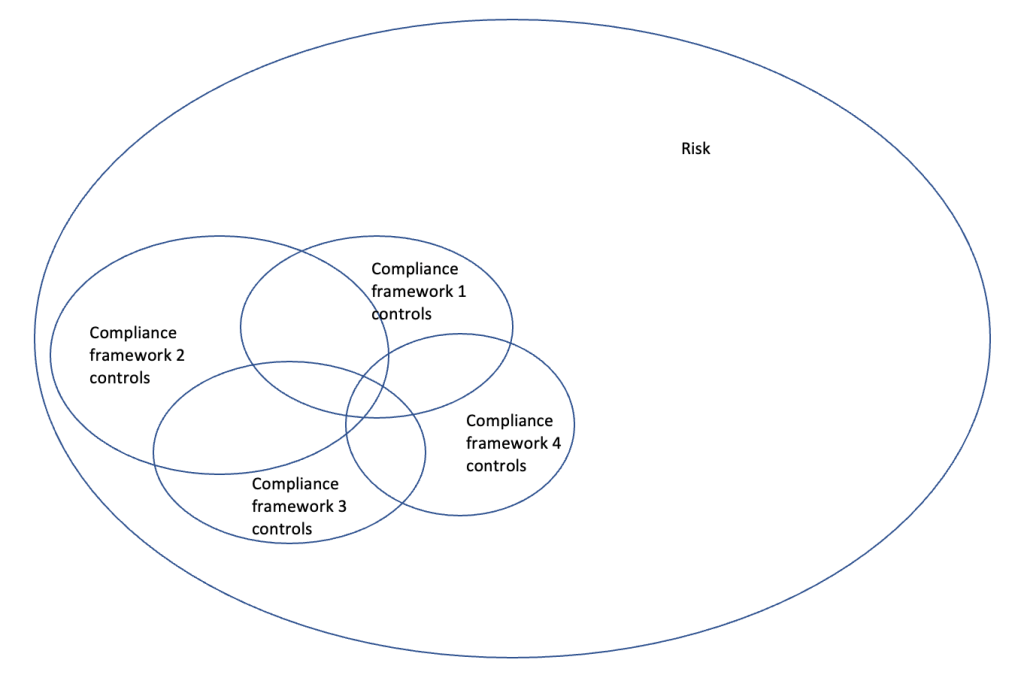
If the company is geographically distributed, noticeable differences usually exist between a number of business units in terms of overall policy framework. The suggestion here is to define a baseline level of security controls across the entire enterprise. The first step in defining these is to understand what we are trying to protect – the assets.
Modern corporations own a wide range of assets that enable them to operate and grow. They broadly include physical and non-physical assets, people and reputation. Engagement from appropriate parts of the business to identify these is important here as potential attacks to these assets might negatively affect the operations.
By understanding the assets we are able to better identify risks, enable effective detection and response, and prioritise controls and remediation efforts better.
It also helps to conduct a bottom-up review of assets to understand what exactly we’ve got there, focusing on the most critical ones and creating and updating asset inventories.
Understanding the asset base and setting standards and guidance for protecting them will focus the efforts and help you prevent and better respond to security issues.
Assets are tightly linked to threat actors, because it’s not enough to know what we need to protect – we also need to know what we are protecting our assets against. Threat actors vary in their motivation and ability and – depending on the company – include nation states, organised crime, insiders, hacktivist, competitors, etc.
A combination of assets and threats helps us to define risks.
Identifying risks and placing them on a heat map helps determine the inherent, residual and target risks. Inherent risks show the level of risk assuming all the controls or remediating measures were absent or failing. Think of it as if security function didn’t exist. It’s not a happy place where we see the majority of risks have high impact and likelihood being in the top right hand side corner of the chart.
Luckily, security function does exist and even if they don’t have a formalised risk management process, they are usually doing a good job in addressing some of these risks.
Current level of risk is taking into account all the controls and remediating measures in place. The initial impact and likelihood is usually reduced and sometimes to an acceptable level agreed by the business. The idea here is although further reduction of impact and likelihood is possible, it might not be cost-effective. In other words, the money might be better spent in addressing other risks.
Target risks is the future state risk level once additional controls and remediation measures are implemented by the security team.
The main takeaway here is that a formalised risk management approach (with accompanying processes and policies) is needed to ensure all risks are identified and tracked over time, and the appropriate resources and efforts are spent on the top priority risks.