
I’m super proud to have written this book. It’s the much improved second edition – and I can’t wait to hear what you think about it.
Please leave an Amazon review if you can – this really helps beat the algorithm, and is much appreciated!
A practical approach
As a CISO who recently led an organisation through successful SOC 2 Type 1 and Type 2 audits, I’d like to share some insights and steps to help others on their journey toward SOC 2 attestation.
SOC 2 may not be for everyone (refer to my blog on compliance frameworks), but it can be useful for organisations dealing with sensitive customer data, particularly in SaaS, as it demonstrates a commitment to security, privacy, and data integrity. The journey toward SOC 2 attestation can be complex, but with careful planning and the right strategies, it’s achievable.
I’m proud to be named CyberPeace Institute‘s Volunteer of the Month.
A big shoutout to CyberPeace for this awesome recognition! It’s been such a rewarding experience to help them in their mission to make the digital world safer for everyone.
The CyberPeace Institute is a non-profit focused on reducing the harm caused by cyberattacks to individuals and communities. Through their CyberPeace Builders program, they offer free cybersecurity support to organisations that need it most, especially those where cyber threats can have a serious impact.
As a volunteer, I’ve had the chance to help for-purpose organisations respond to cyber attacks, develop incident response plans, run security awareness training, perform dark web monitoring and craft essential policies and procedures. Plus, I’ve provided general cyber advice along the way. It’s been an incredible journey being part of a team that’s making a real difference.


Cyber security strategy and execution is one of the top priorities for a CISO. It helps articulate the value of security, provide clarity on short and long term goals and outline a cyber security uplift roadmap.
In this blog I recommend a proven step-by-step guide for developing a cyber strategy.

Asset management is often regarded as the foundation of a security programme. You can’t protect something that you don’t know you have. This extends beyond internal systems to your organisation’s partners. Depending on the line of business, supply chains can get increasingly complex. They include vendors, manufacturers, retailers and distributors in multiple geographies and regulatory regimes. Securing such a network is no easy task and should start with visibility and careful risk management.
I’m often asked what the responsibilities of a CISO or Head of Information Security are. Regardless of the title, the remit of a security leadership role varies from organisation to organisation. At its core, however, they have one thing in common – they enable the businesses to operate securely. Protecting the company brand, managing risk and building customer trust through safeguarding the data they entrusted you with are key.
There are various frameworks out there that can help structure a security programme but it is a job of a security leader to understand the business context and prioritise activities accordingly. I put the below diagram together (inspired by Rafeeq Rehman) to give an idea of some of the key initiatives and responsibilities you could consider. Feel free to adapt and tailor to the needs of your organisation.

You might also find my previous blogs on the first 100 days as a CISO and developing an information security strategy useful.

I previously wrote about how to prepare for the Certified Cloud Security Professional (CCSP) and AWS Certified Solutions Architect – Associate exams. Today, I would like to focus on AWS Security – Specialty.
Exam cost aside, preparing for this specialty can be rather expensive. There is a whole industry around mock practice tests, study books, video tutorials and hands-on labs. Here I’ll aim to outline how to maximise the benefit while minimising costs, focusing on free resources.
Whitepapers, user guides and service FAQs
AWS documentation is arguably the best source of study material out there. I don’t know a single person who passed the exam without reading through at least some of them. Check out the official exam guide for the overview of domains to select the relevant ones. I focused on IAM, KMS, CloudTail, CloudWatch, VPC, Lambda, Inspector, GuardDuty, Athena, Macie and AWS Microsoft AD. At a very minimum, you should read these:
I also wrote about my experience in using security-related AWS services in my blog.
Online courses
Who needs paid for online tutorials when the AWS YouTube channel has a lot of their re:Invent talks available for free? There is literally a video on pretty much every subject you are interested in. There are too many to mention and you could conduct a simple search to find the latest talk on what you want, but I’ll recommend a few to get you started:
If you would rather have a structured online course instead and don’t mind paying a little bit for it, I recommend the Linux Academy and/or A Cloud Guru. I’ve done them both. Personally, I preferred the former as it had some hands-on labs, but A Cloud Guru is shorter and has some good exam tips. Besides, you can try both of them for free for 7 days and decide for yourself.
There is also the official AWS Exam Readiness: AWS Certified Security – Specialty course. It covers the exam structure, gives you tips on tackling questions and provides thorough explanations. I would save this one for last to get a view of your preparedness.
Practice tests
The obvious thing to do is to buy the official practice exam from AWS, right? Well, maybe not. Unless you’ve got it for free for passing one of the other AWS exams previously, you might be better off finding an alternative. It only includes 20 questions (which works out at $2 per question plus tax), and you don’t get to see the answers! Instead, you are presented with a pass/fail summary that gives you the overall percentage broken down by exam domains. You might be better off using the free 15 questions from Whizlabs, although I can’t recommend their paid products. Practice tests are also included in the Linux Academy and A Cloud Guru courses I mentioned above. Plus, the free official Exam Readiness course also comes with 24 questions with answers and explanations at the end. That should be enough to give you the feel for types of question on the exam.
Getting ready
When revising, I found some good notes and a mindmap from other students on the internet. You can also go through a set of flashcards (e.g. on Quizlet) to recap on what you’ve learned.
With all this preparation, don’t lose track of why you are doing it in the first place: gaining the skills that you can apply in practice. The exam gives a good indication of your weaker areas and encourages you to fill these gaps. The best way to do this is, of course, through hands-on experience. If your organisation relies on AWS, find ways to apply the newly acquired knowledge there to make your cloud infrastructure more secure. If that’s not an option, there is always the Free Tier, where you can put your skills into practice. Finally, the Linux Academy (and some other providers) for a small cost offer you some hands-on labs and even a whole sandboxed playground for you to experiment in.
AWS constantly evolve and refine their services, and add new ones too. Keep this in mind while studying, as things move pretty fast in the cloud world. This also means that your learning is never finished, even if you pass the exam. But I think this is a good thing and I’m sure you agree!
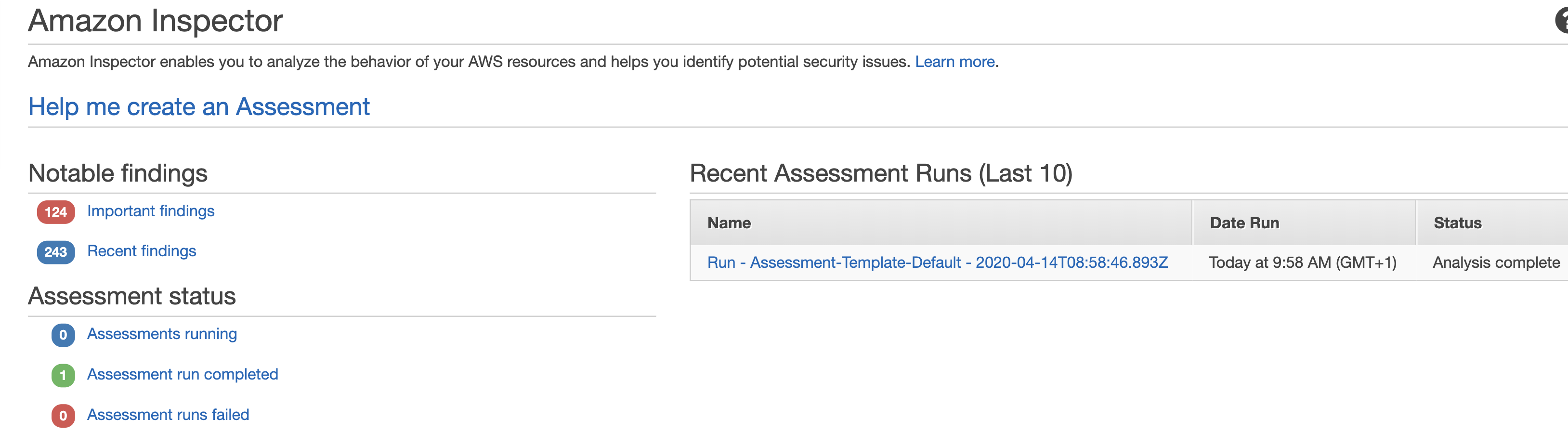
If you rely on EC2 instances in at least some parts of your cloud infrastructure, it is important to reduce the attack surface by hardening them. You might want to check out my previous blogs on GuardDuty, Config, IAM and CloudTrail for other tips on securing your AWS infrastructure. But today we are going to be focusing on yet another Amazon service – Inspector.
To start with, we need to make sure the Inspector Agent is installed on our EC2 instances. There are a couple of ways of doing this and I suggest simply using the Inspector service Advance Setup option. In addition, you can specify the instances you want to include in your scan as well as its duration and frequency. You can also select the rules packages to scan against.
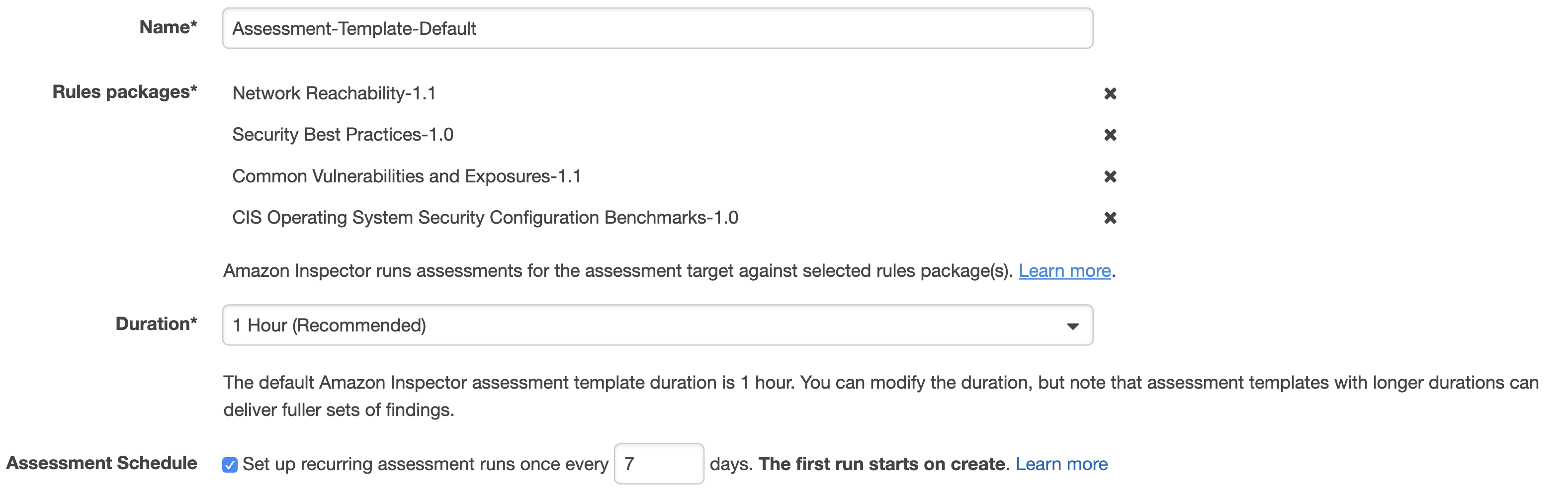
After the agent is installed, the scan will commence in line with the configuration you specified in the previous step. You will then be able to download the report detailing the findings.
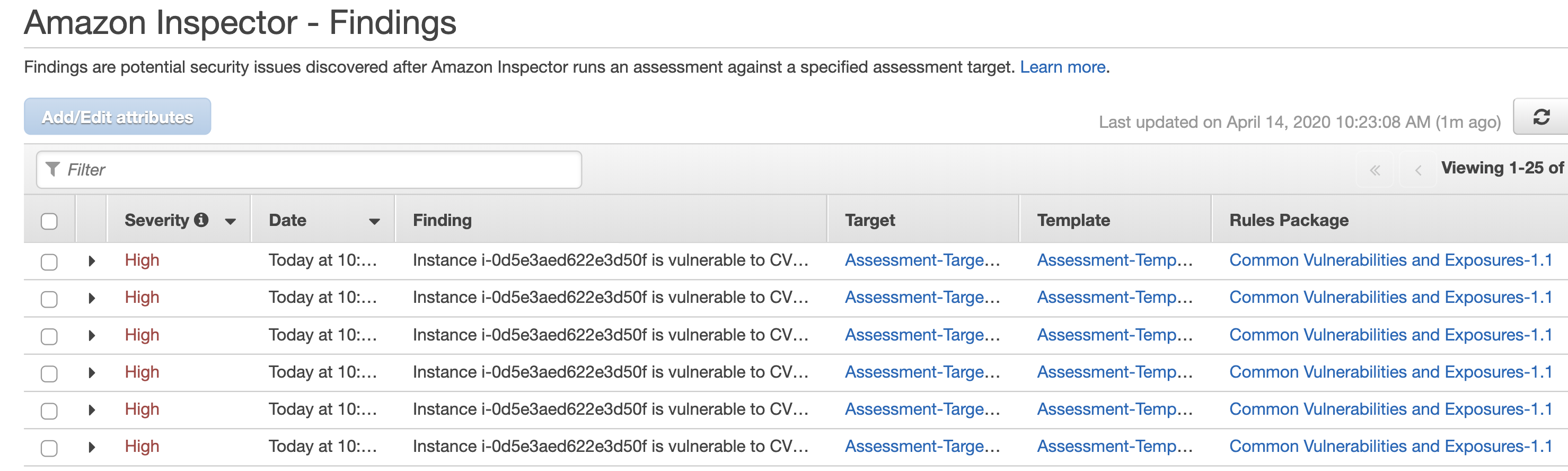
The above setup gives you everything you need to get started but there is certainly room for improvement.
It is not always convenient to go to the Inspector dashboard itself to check for discovered vulnerabilities. Instead, I recommend creating an SNS Topic which will be notified if Inspector finds new weaknesses. You can go a step further and, in the true DevSecOps way, set up a Lambda function that will automatically remediate Inspector findings on your behalf and subscribe it to this topic. AWS kindly open sourced a Lambda job (Python script) that automatically patches EC2 instances when an Inspector assessment generates a CVE finding.
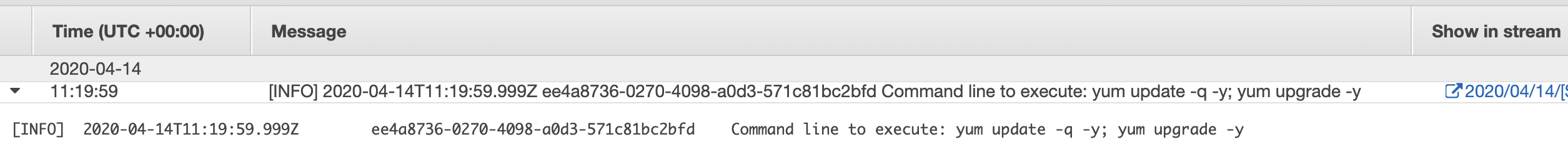
You can see how Lambda is doing its magic installing updates in the CloudWatch Logs:
Or you can connect to your EC2 instance directly and check yum logs:
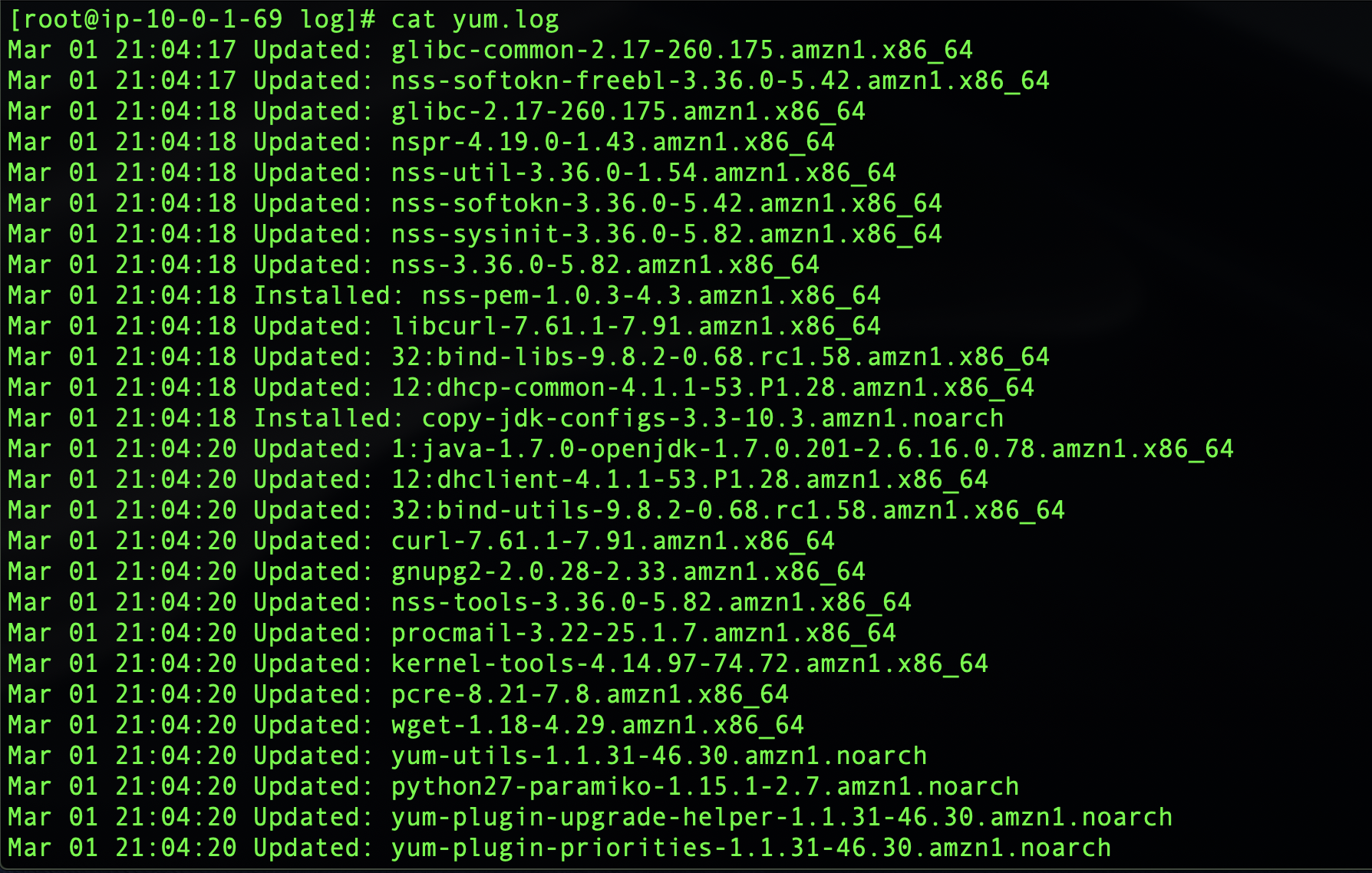
You will see a number of packages updated automatically when the Lambda function is triggered based on the Inspector CVE findings. The actual list will of course depend on how many updates you are missing and will correspond to the CloudWatch logs.
You can run scans periodically and still choose to receive the notifications but the fact that security vulnerabilities are being discovered and remediated automatically, even as you sleep, should give you at least some peace of mind.
 If you work for or (even better) co-founded a tech startup, you are already busy. Hopefully not too busy to completely ignore security, but definitely busy enough to implement one of the industrial security frameworks, like the NIST Cybersecurity Framework (CSF). Although the CSF and other standards are useful, implementing them in a small company might be resource intensive.
If you work for or (even better) co-founded a tech startup, you are already busy. Hopefully not too busy to completely ignore security, but definitely busy enough to implement one of the industrial security frameworks, like the NIST Cybersecurity Framework (CSF). Although the CSF and other standards are useful, implementing them in a small company might be resource intensive.
I previously wrote about security for startups. In this blog, I would like to share some ideas for activities you might consider (in no particular order) instead of implementing a security standard straight away. The individual elements and priorities will, of course, vary depending on your business type and needs and this list is not exhaustive.
Product security
Information security underpins all products and services to offer customers an innovative and frictionless experience.
Cloud infrastructure security
To deliver resilient and secure service to build customer trust.
Operations security
To prevent regulatory fines, potential litigation and loss of customer trust due to accidental mishandling, external system compromise or insider threat leading to exposure of customer personal data.
Cyber resilience
To prepare for, respond to and recover from cyber attacks while delivering a consistent level of service to customers.
Compliance and data protection
To demonstrate to business partners, regulators, suppliers and customers the commitment to security and privacy and act as a brand differentiator. To prevent revenue loss and reputational damage due to fines and unwanted media attention as a result of GDPR non compliance.
Image by Lennon Shimokawa.

In this blog I’m going to build on my previous posts on agile security, DevSecOps culture and managing vulnerabilities in open source libraries to talk about automating application security testing.