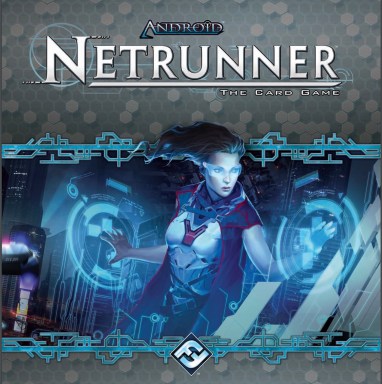
Android: Netrunner is a two-player card game that can teach you a great deal about cyber security. It’s fun to play too.
Bad news first: although initially intended as a ‘living card game’ with constantly evolving gameplay, this game has now been discontinued, so no expansions will be published, limiting the community interest, ongoing deckbuilding and tournaments.
Now to the good news, which is pretty much the rest of this blog. None of the above can stop you from enjoying this great game. You can still acquire the initial core set which contains all you need for casual play.
The premise of this game is simple: mega corporations control all aspects of our lives and hackers (known as runners) oppose them. I know it was supposed to be set in the dystopian cyberpunk future, but some of the elements of it are coming to life sooner than expected since the original game release in 1996.

The runners vary in their abilities that closely align to their motivation: money, intellectual curiosity, disdain for corporations. Corporations have their core competencies too. Again, just like in real life. The core set I mentioned earlier consists of seven pre-built, and balanced by creators, decks: three for runners and four for corporations with their unique play styles.
The game is asymmetrical with different win conditions: runners are trying to hack into corporations’ networks to steal sensitive information (known as agendas in the game) and corporations are aiming to defend their assets to achieve their objectives (advance agendas). This masterfully highlights the red team versus blue team tension commonplace in today’s infosec community.

A corporation has to adapt to evolving threats posed by hackers installing protective devices and conducting defensive operations all the while generating revenue to fund these projects and reach their targets to win the game. It’s not only about defence for the corporation either. Today’s “hacking back” debate got apparently settled in the future, with corporations being able to trap, tag and trace hackers to inflict real damage, as an alternative win condition.
Runners differ vastly in methods to penetrate corporation’s defences and have to take care of an economy of their own: all these cutting edge hacking consoles cost money and memory units. Example cards in runner’s toolbox sometimes closely resemble modern methods (e.g. siphoning off corp’s accounts) and sometimes gaze far into the future with brain-machine interfaces to speed up the process.
Basic rules are simple but there are plenty of intricate details that make players think about strategy and tactics. It’s a game of bluff, risk and careful calculation. There’s also an element of chance in it, which teaches you to be able to make the best use of resources you currently have and adapt accordingly.
It’s not an educational game but you can learn some interesting security concepts while playing, as you are forced to think like a hacker taking chances and exploiting weaknesses or a defender trying to protect your secrets. All you need is the deck of cards and someone to play with.