Picture an easy Sunday morning. It’s sunny and quiet with only birds chirping outside. You make yourself a cup of coffee and sit on the sofa to catch-up on what’s happening in the world. You open your favourite news site and here it is – first story of the day in large font.
Breaking news: massive data breach! It’s your company in the headline.
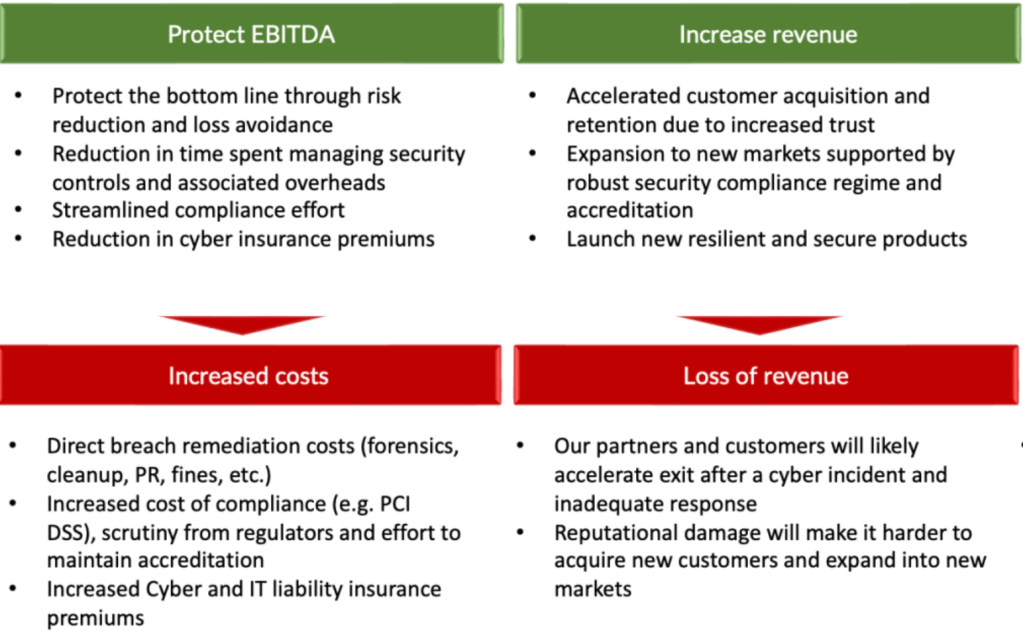
This is the modern reality, cyber attacks are becoming increasingly common and it’s no longer a matter of if but when.
How do you manage this PR nightmare? What do you tell the media? Can you regain the trust of your customers and partners?
These are not the questions you want to be thinking about in the middle of a crisis. The real story begins way before that. It starts with responsible data management practices and securing people’s information.